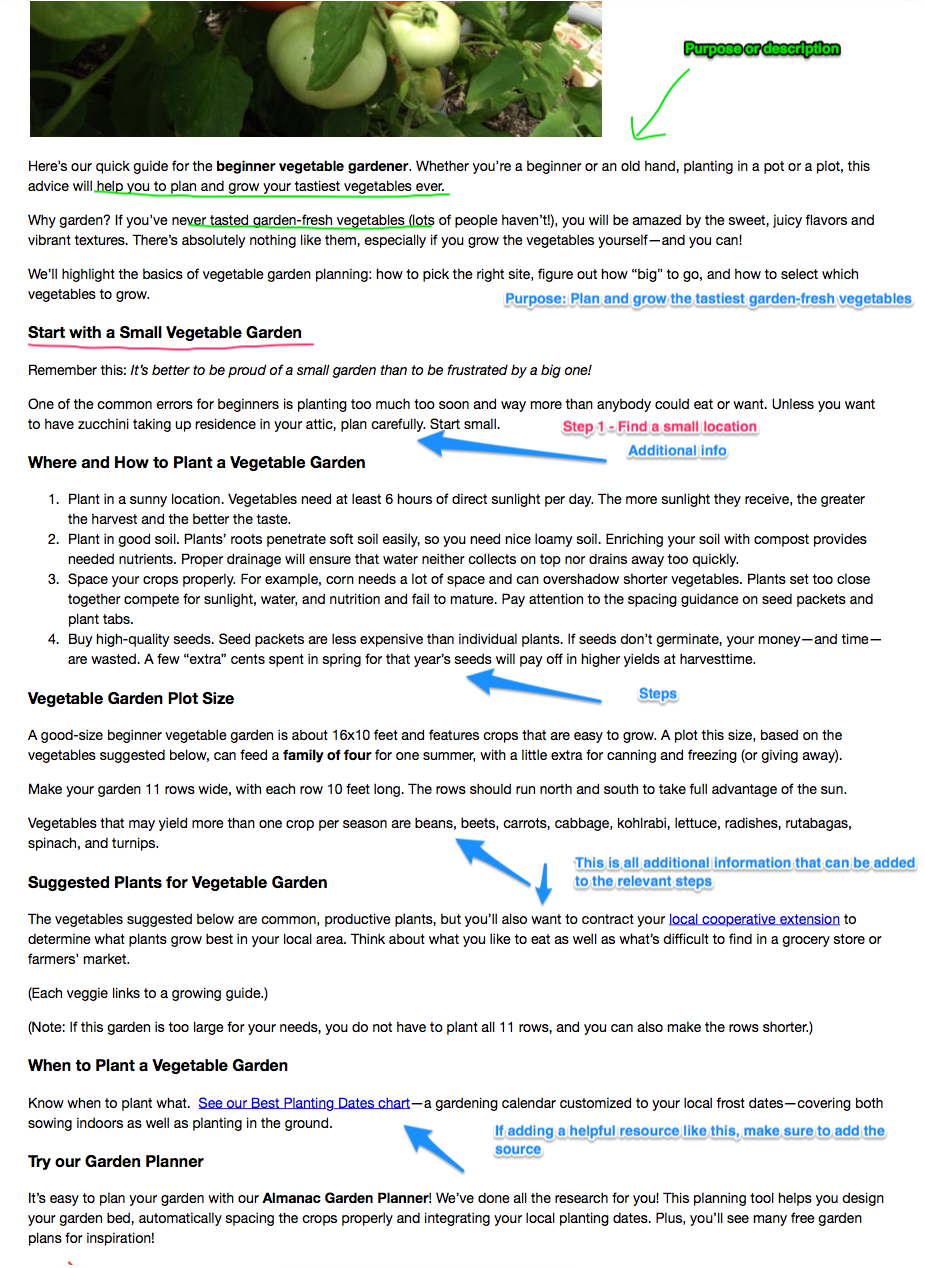
Patch management is a careful process. It'd be reckless to deploy untested patches across your whole organization, so it's often done with a test group beforehand.
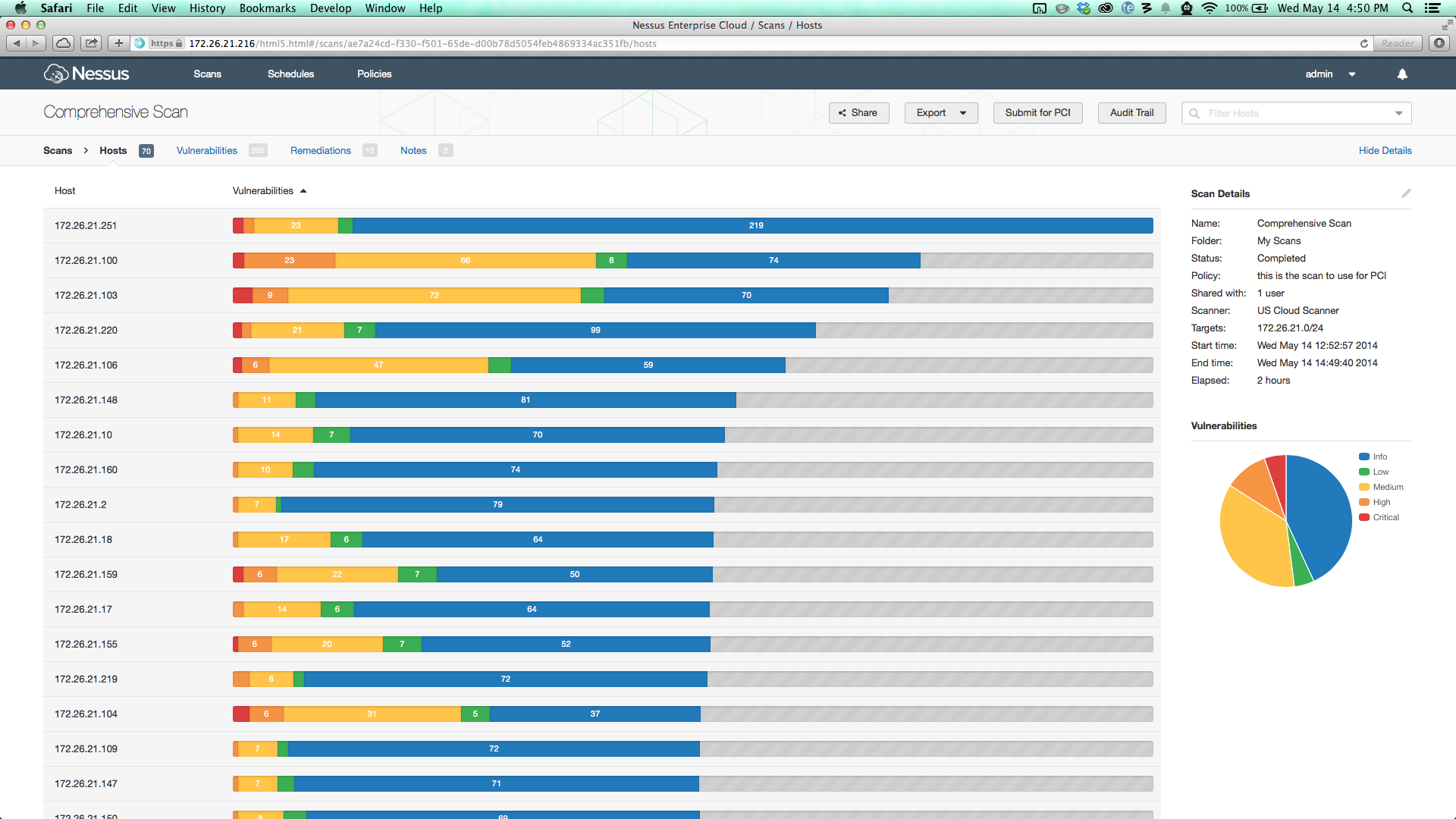
A vulnerability scanner will highlight the need for patching automatically, but the reporting and deploying needs human intervention.
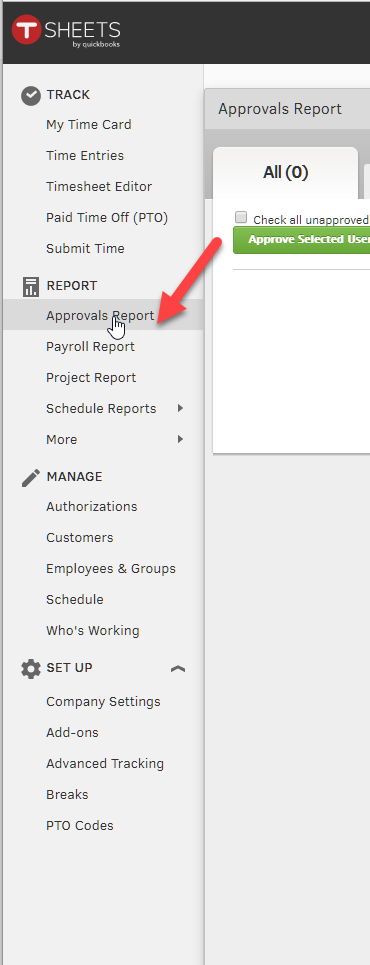
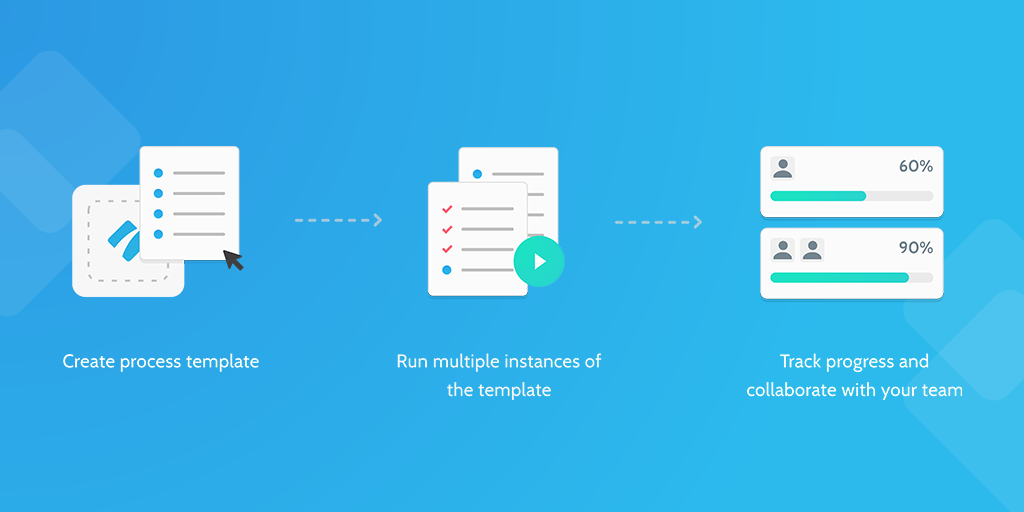
In this process, you'll be able to structure your patch testing and deployment in a way that reduces the risk of error. It can also link into our scheduled maintenance process, so you can issue notifications of any expected disruptions.