Server-side events logs and everything that comes with it can be a big stress.
With SQL Server logging compliance standards tighter than ever in the face of recent data security acts such as HIPAA, PCI DSS, and SOX, there is often so much that goes into the preparation for an SQL Server Audit that it can be confusing to keep track of everything.
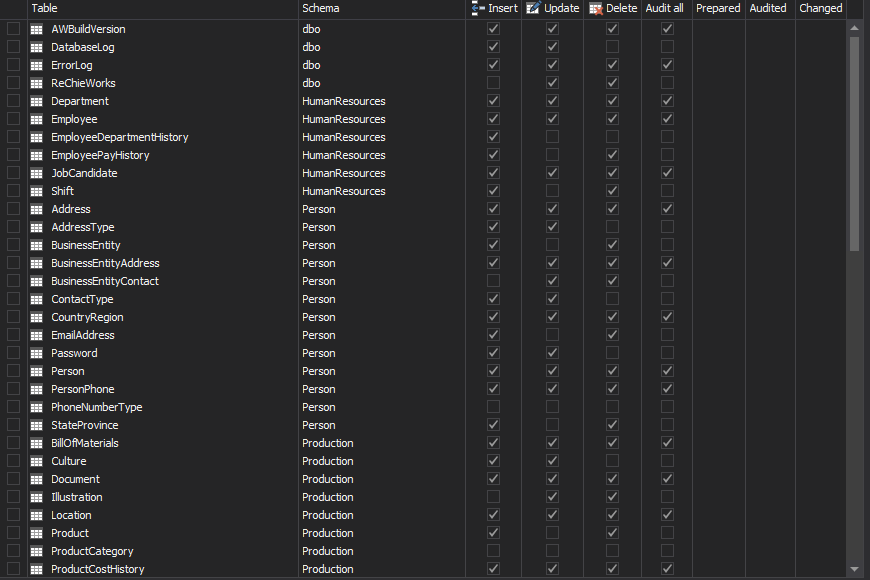
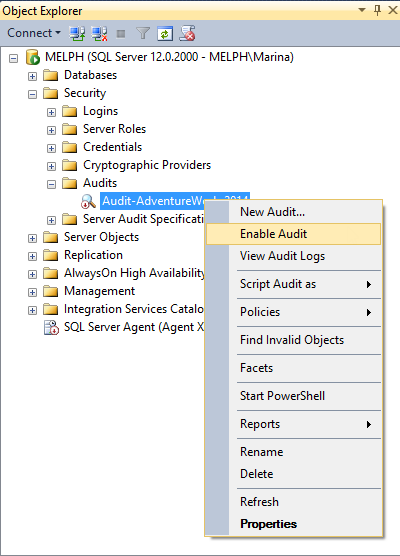
On the other hand, the SQL Server Audit process has been greatly improved in recent years by the addition of Extended Events logs, allowing administrators to audit everything that happens on each server, from large-scale changes to system settings right down to which user modified what specific value in a particular database at any given time.
But still, despite all of these improvements to the server auditing process, it can still be daunting to get started without a formal process already in place.
Alongside events log best practices, there are a number of related tasks you should be incorporating into any routine server best practice check, like system updates and data encryption. These additional checks serve to support the audit process as well as harden overall server security.
This checklist is designed to give you a head-start for preparation ahead of and including an SQL Server Audit. Though we've been rigorous, this checklist is just an example and is by no means exhaustive of every SQL Server security parameter.
Nonetheless, let's dive right in!