Turn every policy into automated workflows with built-in enforcement and audit-ready proof.
Vendor Onboarding Checklist
A vendor onboarding compliance checklist is the control path a company uses to approve a new supplier before work starts, payment begins, or system access is granted. A practical vendor onboarding checklist does more than collect forms. It assigns owners, verifies risk, captures evidence, and proves that procurement, finance, legal, security, and compliance followed the same process every time.
That matters because vendor onboarding is where many third-party risks first enter the business. A supplier may touch customer data, handle payments, deliver a critical service, process employee information, or create regulatory exposure. If the review happens in email and spreadsheets, the company may approve the vendor but still fail to prove what was checked.
This guide gives you a vendor onboarding checklist you can use as a working control framework. It covers intake, documentation, tax, sanctions, security, privacy, insurance, contract approval, risk tiering, and ongoing monitoring. It also shows how to turn the checklist into an auditable workflow in Process Street.
In this article, we are going to cover everything you need to know about vendor onboarding compliance checklists, including:
- What a vendor onboarding compliance checklist is
- Vendor onboarding checklist: intake and ownership
- Documents to collect before vendor approval
- Compliance checks to complete before vendor approval
- Risk-based routing and approvals
- How to turn the vendor onboarding compliance checklist into an auditable workflow
- Common vendor onboarding mistakes
- How Process Street helps vendor onboarding compliance
- FAQs
What a vendor onboarding compliance checklist is
A vendor onboarding compliance checklist is a repeatable set of tasks for collecting, validating, approving, and monitoring a new vendor. It should answer five basic questions: who requested the vendor, what the vendor will do, what risk the vendor creates, which evidence proves the risk was reviewed, and who approved the relationship.
The checklist is not the same thing as a vendor form. A form collects information. A checklist controls the work around that information. It decides when a vendor setup checklist starts, which reviewers are required, what blocks approval, and what must happen after the vendor is live.
What the checklist should prove
The best checklist creates proof in the normal course of work. If a vendor handles personal data, the checklist should show that privacy and security reviewed the relationship. If the vendor gets paid, the checklist should show that tax documentation and payment controls were completed. If the vendor supports a regulated process, the checklist should show that compliance approved the risk before launch.
- The business owner documented the need and scope of work.
- Procurement or vendor management verified the supplier profile.
- Finance collected required tax and payment documentation.
- Legal approved the contract path and required clauses.
- Security and privacy reviewed data access, if applicable.
- Compliance confirmed sanctions, licensing, regulatory, and policy requirements.
- A named approver accepted the residual risk before activation.
That proof is important for audits, vendor disputes, regulatory exams, and internal reviews. NIST supply-chain guidance emphasizes identifying, assessing, and managing cybersecurity supply-chain risk across the organization, which is difficult to do when vendor files are scattered across inboxes and shared drives. See NIST SP 800-161 Rev. 1 for the underlying supply-chain risk management concept.
Vendor onboarding checklist: intake and ownership
The checklist starts before due diligence. Someone has to explain why the vendor is needed, what the vendor will touch, and who owns the relationship after approval. Without this intake step, compliance teams end up reviewing incomplete requests and procurement teams chase basic context after the fact.
Start with a clear request
Use an intake task to capture the vendor name, business owner, department, requested service, expected start date, expected spend band, systems involved, data categories, locations served, and whether the vendor is replacing an existing supplier. Link the request to any selection work already completed, such as a vendor selection process or supplier selection and evaluation process.
The intake task should also ask what would happen if the vendor failed. A vendor that ships office supplies does not need the same review as a payroll provider, payment processor, cloud service, claims administrator, or outsourced support team. The business impact answer helps the workflow route the vendor correctly.
Assign one accountable owner
Every vendor needs one business owner who remains accountable after the onboarding checklist closes. That owner confirms the vendor is still needed, reviews performance, answers renewal questions, and helps compliance collect updated evidence. Shared ownership usually means no ownership.
- Business owner: defines need, scope, and acceptance criteria.
- Procurement owner: manages supplier record, commercial path, and vendor communications.
- Finance owner: validates tax, banking, and payment setup requirements.
- Legal owner: reviews contract terms, data clauses, indemnity, and termination rights.
- Security or privacy owner: reviews data access, integrations, certifications, and questionnaires.
- Compliance owner: reviews sanctions, licensing, policy fit, and audit evidence.
Vendor onboarding checklist documents to collect before approval
Document collection is where most vendor onboarding checklists become bloated. The goal is not to collect every possible file. The goal is to collect the minimum evidence needed to approve the vendor based on the risk they create.
A low-risk office vendor might only need tax and contract documentation. A high-risk technology vendor may need security certifications, data processing terms, insurance, penetration test summaries, incident response details, and a named escalation path. A risk-based checklist keeps both paths in one system without forcing every vendor through the longest possible review.
Core vendor profile documents
- Legal entity name, registered address, and primary contact.
- Business registration or incorporation evidence where required.
- Beneficial ownership or parent company information for higher-risk vendors.
- Service description, statement of work, purchase order, or request summary.
- Tax documentation, such as Form W-9 for U.S. vendors or the relevant local equivalent.
- Payment setup documentation, reviewed through a secure finance process.
For U.S. tax reporting, the IRS explains that Form W-9 is used to provide the correct taxpayer identification number to a requester that must file an information return. The checklist should capture the form, verify it was reviewed, and document any exception path before vendor activation.
Risk and compliance documents
- Certificate of insurance, including general liability, cyber liability, or professional liability where relevant.
- Information security questionnaire or security review summary.
- SOC 2, ISO 27001, PCI, HIPAA, or other certification evidence where applicable.
- Privacy policy, data processing agreement, subprocessors list, and data retention details.
- Business continuity and incident response summaries for vendors that support critical services.
- Licenses, permits, professional certifications, or regulatory attestations required for the service.
If your organization already uses a vendor risk assessment template, connect it to this document collection step. The risk assessment should decide which documents are required, not sit in a separate file after documents have already been requested.
Compliance checks to complete before vendor approval

The compliance review confirms that the vendor can be approved under your policy, risk appetite, and legal obligations. This is where the vendor onboarding checklist moves from administrative setup to control execution.
Sanctions and restricted-party screening
Screen vendors and beneficial owners against applicable sanctions and restricted-party lists before approval. In the U.S., teams often rely on OFAC data and related watchlist tools. OFAC provides public sanctions list resources, including its sanctions list search and list data. The checklist should record the screening date, the reviewer, the tool or source used, and the result.
Do not treat screening as a one-time checkbox for high-risk vendors. If the vendor operates internationally, touches regulated transactions, or receives recurring payments, schedule periodic rescreening. The onboarding checklist should create that future review task before the vendor goes live.
Security and privacy review
Security review should follow data access. Ask what systems the vendor will access, what data they will process, how data moves, where it is stored, who can access it, and what happens at termination. The FTC Safeguards Rule guidance states that covered companies must take steps to ensure service providers safeguard customer information in their care. The FTC also says companies should select service providers with the skills and experience to maintain appropriate safeguards. See the FTC Safeguards Rule business guidance.
For technology vendors, connect the review to a supplier risk assessment or security questionnaire. Store the decision, not just the file. A useful checklist records whether security approved, approved with conditions, rejected, or escalated the vendor.
Insurance, legal, and contract checks
Insurance and contract review should happen before the vendor receives access or starts work. The checklist should confirm coverage types, policy limits, additional insured requirements, service levels, confidentiality clauses, data protection terms, right-to-audit language, termination rights, and any required compliance representations. Contract-heavy relationships can route into a vendor contract negotiation workflow so legal review is visible and assigned.
Risk-based routing and approvals
A single static checklist breaks down because vendor risk is not equal. Risk-based routing lets you use one standard process while changing the depth of review based on the vendor profile.
A simple risk-tier model
- Low risk: limited spend, no sensitive data, no critical operations, no regulated service.
- Medium risk: recurring service, moderate spend, limited internal access, or operational dependency.
- High risk: sensitive data, financial controls, regulated activity, critical service, system integration, or customer-facing impact.
- Critical risk: outsourced core function, privileged access, material business continuity impact, or regulator-visible service.
Use the risk tier to trigger conditional tasks. Low-risk vendors can move through a shorter approval path. High-risk and critical vendors should require enhanced due diligence, legal approval, security approval, documented residual risk acceptance, and a monitoring schedule. This is where a third party risk management workflow connects naturally to vendor onboarding.
Approval rules by risk
Approvals should be explicit. The checklist should show who approved the vendor, what they reviewed, whether exceptions were granted, and what conditions remain open. For a low-risk vendor, a procurement or business owner approval may be enough. For a high-risk vendor, require finance, legal, security, compliance, and executive risk acceptance when policy calls for it.
The approval record matters later. If a vendor has an incident, misses a control, or appears in an audit sample, you need more than a Slack message saying someone was fine with it. You need the route, evidence, decision, and timestamp in one place.
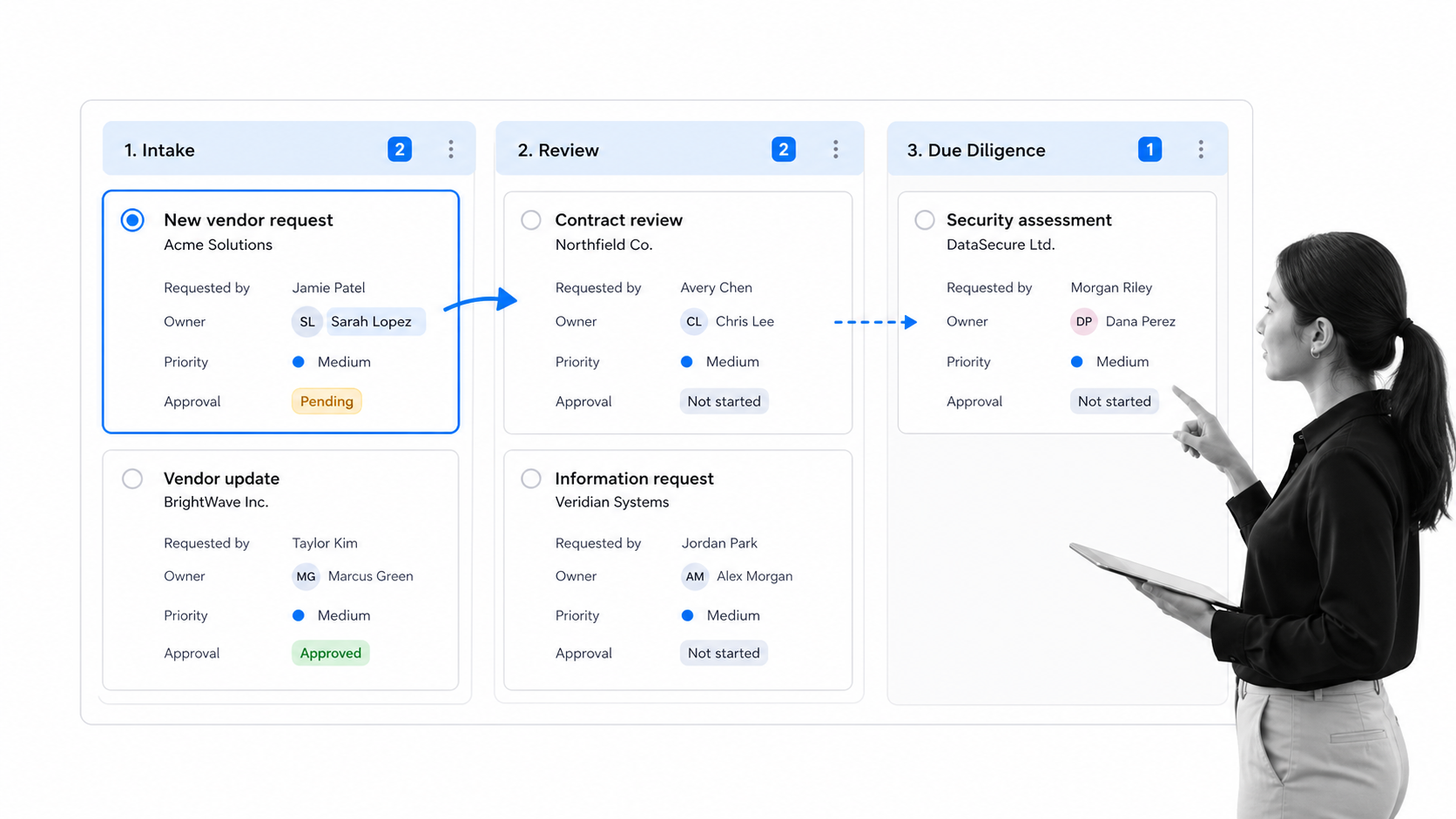
How to turn the vendor onboarding compliance checklist into an auditable workflow

A checklist becomes auditable when it is run as a workflow, not when it is stored as a document. The workflow should assign each task, enforce required fields, collect files, block skipped approvals, and retain a record of what happened.
Build the workflow around control points
Start by separating the checklist into control points: intake, profile validation, document collection, tax review, sanctions screening, security review, privacy review, contract review, risk tiering, approval, activation, and monitoring setup. Each control point should have an owner, required evidence, completion criteria, and escalation path.
You can use the vendor setup checklist as a practical starting point, then add risk-specific branches for security, privacy, legal, and compliance. For supplier-heavy teams, the vendor management supplier evaluation workflow helps evaluate capacity, quality, stability, and ethical fit before onboarding moves forward.
Automate evidence and reminders
Manual follow-up is the hidden cost of vendor onboarding. Automate reminders for missing files, overdue approvals, expiring insurance, annual reviews, and rescreening. The workflow should also write the final vendor record to the right system of record, whether that is procurement, finance, ERP, vendor management, or a shared compliance repository.
Process Street supports this by turning policy into assigned tasks, forms, conditional logic, approvals, due dates, and audit trails. The workflow template gallery guidance is a useful starting point if your team wants to import a template, customize the steps, and run it as a repeatable workflow.
Common vendor onboarding mistakes
Most vendor onboarding failures come from gaps between teams. Procurement thinks legal is reviewing the contract. Legal thinks security already reviewed data access. Finance creates the vendor record before tax documentation is complete. Compliance only sees the vendor when an audit asks for evidence.
Mistake 1: treating onboarding as form collection
Forms are necessary, but they are not enough. A strong vendor onboarding checklist verifies the information, assigns review ownership, and records approval decisions. If the checklist only says “collect W-9” or “collect insurance,” it misses the control question: who reviewed the file and what decision did they make?
Mistake 2: using the same path for every vendor
One path creates two problems. Low-risk vendors get slowed down by unnecessary review, and high-risk vendors slip through because the checklist cannot branch. Risk-based conditional logic solves this by changing the work based on data access, spend, geography, service type, and operational criticality.
Mistake 3: forgetting ongoing monitoring
Vendor onboarding should create future obligations. Insurance expires. Certifications need renewal. Sanctions status can change. Performance can degrade. Data access can expand. Use the checklist to schedule periodic reviews and route unresolved issues into a process risk assessment template or corrective action workflow.
How Process Street helps vendor onboarding compliance
Process Street is built for repeatable, compliance-sensitive workflows where skipped steps create risk. A vendor onboarding checklist in Process Street can require fields, route tasks by risk, collect files, trigger approvals, automate reminders, and retain the audit trail without forcing the team to manage the process from spreadsheets.
For compliance teams, the value is proof. Every task has an owner. Every approval has a timestamp. Every file sits with the step that required it. Every exception can be reviewed later. If the vendor moves from onboarding into broader oversight, Process Street can connect the onboarding workflow to third party risk management software, vendor management software, policy workflows, and ongoing monitoring.
What to automate first
- Start with vendor request intake and ownership assignment.
- Add conditional routing for data access, risk tier, spend band, and regulated service type.
- Require tax, insurance, security, privacy, and contract evidence before approval.
- Use approvals to block activation until the right owners sign off.
- Schedule recurring reviews, document refreshes, and sanctions rescreening before closing the workflow.
The result is not just a cleaner checklist. It is a controlled vendor onboarding process that helps teams enforce policy, track steps, and prove compliance by default.
FAQs
What is a vendor onboarding checklist?
A vendor onboarding checklist is a repeatable set of tasks for approving a new supplier before work starts, access is granted, or payment begins. It usually covers intake, documentation, tax, security, privacy, legal, compliance, approvals, and monitoring setup.
What should be included in a vendor onboarding compliance checklist?
A vendor onboarding compliance checklist should include business need, owner assignment, vendor profile, tax forms, payment controls, sanctions screening, insurance, security review, privacy review, contract approval, risk tiering, final approval, and recurring review tasks.
Who owns vendor onboarding?
Vendor onboarding is usually shared by procurement, finance, legal, security, compliance, and the business owner. The best operating model gives each step a clear owner and keeps one business owner accountable for the vendor relationship after approval.
How often should vendors be reviewed after onboarding?
Review cadence should follow risk. Low-risk vendors may be reviewed annually or at renewal, while high-risk vendors may need quarterly monitoring, annual security evidence, insurance refreshes, sanctions rescreening, and documented performance reviews.
How does automation improve vendor onboarding compliance?
Automation improves vendor onboarding compliance by assigning tasks, enforcing required fields, routing high-risk vendors to the right reviewers, sending reminders, collecting evidence, blocking skipped approvals, and keeping an audit trail for every decision.