 Being secure online is of greater and greater importance. As businesses operate almost entirely online and sensitive information finds itself living full time in the cloud, we have to make sure we have appropriate measures in place to keep information safe.
Being secure online is of greater and greater importance. As businesses operate almost entirely online and sensitive information finds itself living full time in the cloud, we have to make sure we have appropriate measures in place to keep information safe.
One tried and tested way of promoting security is the use of failsafes in login systems. This is what’s referred to as Two Factor Authentication (2FA) or Multi Factor Authentication (MFA).
This means that someone could get hold of your email and password, yet your data is still kept safe.
Whether you’re already familiar with the terminology or not, you’re certainly familiar with the concept.
In this Process Street article, we’ll look at:
- Why is two factor authentication important?
- What two factor authentication is
- The 2 classic examples of 2FA: banks and Apple
- How you can implement two factor authentication in your team
- Free Process Street template: How to enable two factor authentication with Authy, Google, and Slack
Why is two factor authentication important?

This is really simple but we should spell it out.
If you use an email address and password to secure your access to important information then all a person needs in order to access that information is your login details.
There is no double-check in place. Someone could access your email account, for example, and you won’t know.
Moreover, depending on the study, somewhere between 50 and 80% of people use the same password for different sites. Most also use the same email address across a whole load of platforms.
This means if someone gets your login details they might be able to access multiple platforms you have accounts on. If you manage a team, then even if you take strong IT security precautions there is no guarantee that all your team do.
In fact, even if you’re secure with your information, data leaks happen all the time.
The 2016 US election had compromised email accounts as a central part of the spectacle and treasure troves of information were leaked online. The Equifax leak shortly after resulted in huge amounts of sensitive information accessed by hackers – the details of 17.6 million driver’s licenses included.
Whether you’re thinking of how to make your organization more secure, or just your personal accounts, setting up a failsafe can fight back against malicious attempts to access your data.
In the age of GDPR and more digital legislation coming, it is vital you keep your organization secure too – to show you’ve taken all reasonable steps to protect your customer’s data. We’re doing it at Process Street, and recommend you do too!
One answer to this is two factor authentication.
What is two factor authentication?
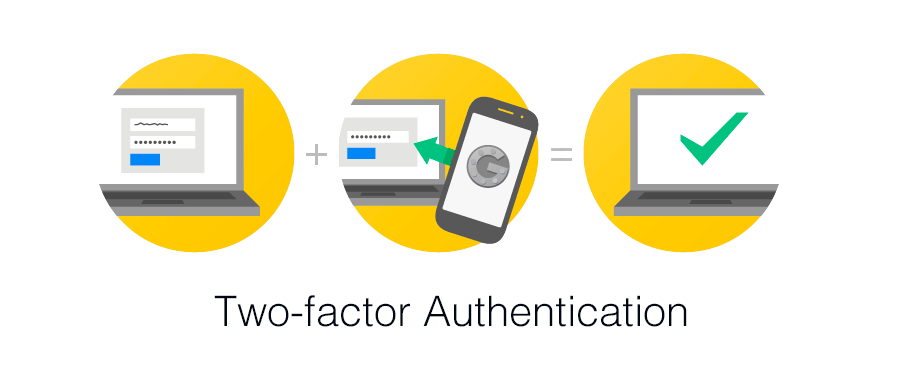
Two factor authentication is a form of multi factor authentication where a person confirms their identity using two different pieces of evidence.
Normally, websites which you have to log into will ask you for your username or email and then the corresponding password. This sounds like two pieces of evidence, but it doesn’t qualify to be called two factor authentication.
The reason is that 2FA is not based on how many pieces of evidence you have, per se, but how many different types of evidence you have. An email address and a password are both the same type of information, even if one is normally more secret than the other.
An email or password both fall into the category of being something the user knows – and that isn’t sufficient for 2FA.
There are three types of evidence which can be combined to deliver two factor authentication:
Something the user knows
This is what you normally think of when providing information to log into a platform. You remember this information and it can be used to grant you access.
Examples include:
- Email address
- Password
- PIN code
- Answers to security questions
Something the user has
This often refers to something physical which a person may have which is unlikely to have been replicated. It can refer to physical objects or can refer to software elements.
Examples include:
- Bank cards
- Keys
- Mobile phone
- Tokens
Something inherent to the user
This is a little less common but is growing in terms of popularity. Being inherent to the user refers to something specific about that individual which would be very hard to copy or fake. This is the more sci-fi of the available options.
Examples include:
- Biometrics
- Fingerprints
- Retina scans
- Voice recognition
How does it work in practice?
We combine these elements to create security. Two factor authentication is a subdivision of multi factor authentication simply because it utilizes more than one type of identifier. Using more than two types is difficult and can be seen as intrusive by the user, or can be impractical at this moment in time for general commercial use.
For something to qualify as 2FA it must use at least two of the above types of evidence.
So, imagine you have set up your email account with 2FA. Some nasty person has found your email and password from a company leak. The person tries to log in to your account.
Do they get in?
No. Because they need the code which was sent to your mobile phone.
Now you not only know that your account is secure, but you also know someone has attempted to access your account. The text your received keeps your data safe and also works like an alert system.
The 2 classic examples of 2FA: banks and Apple
When you go to withdraw money from a cash machine or you pay for something using chip and pin, you are employing two factor authentication.
You physically possess the card necessary to initiate the operation and you remember the PIN as a knowledge based evidence that you are the real owner of that card.
This might be one of the most common and well established forms of 2FA in use.
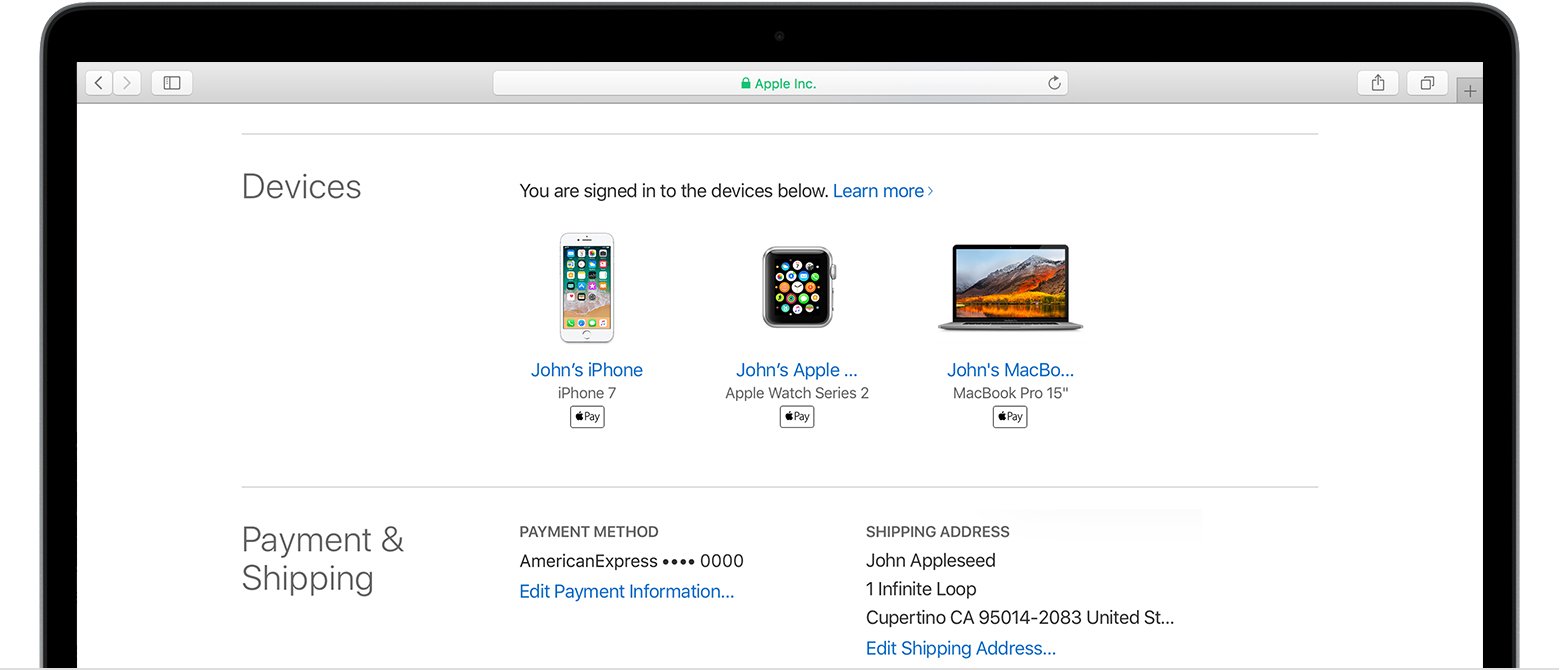
In terms of software, we can use Apple as an example.
I like this example because so much information is shared across Apple devices and they sync up with each other in a whole range of convenient ways. Instead of just logging into a website you occasionally use, if you’re an iPhone or Macbook user your access to your device is a daily part of your life.
As they outline on their support page:
With two-factor authentication, your account can only be accessed on devices you trust, like your iPhone, iPad, or Mac. When you want to sign in to a new device for the first time, you’ll need to provide two pieces of information—your password and the six-digit verification code that’s automatically displayed on your trusted devices.
This two-factor authentication protects you from another device maliciously joining that network of connected devices.
However, software companies can only do so much for us. We have to participate in security measures too. If I were to leave my passwords written down on my desk in a shared office with my devices lying around as I pop off to lunch, I’m undoing all the structures Apple have put in place for my security.
Apple’s 4 points of advice for a user to leverage 2FA effectively for their benefit are:
- Remember your Apple ID password.
- Use a device passcode on all your devices.
- Keep your trusted phone number(s) up to date.
- Keep your trusted devices physically secure.
How to implement two factor authentication on your team
There are two steps to implementing two factor authentication on your team.
First, you have to set it up via the administration panel.
Second, all your team need to set up 2FA for their logins.
As Google’s email and work platform is a popular one, we’ll walk through how to do this in GSuite below.
We’ll also then look at how to approach it for Office365 and how to set up the mobile app Authy for 2FA too.
Finally, we’ll give you an actionable Process Street template which you or your team could use to guide you through the 2FA process!
How to setup two factor authentication for GSuite
Log into your GSuite account and enter into the Admin panel. You can access this via the same screen with the shortcuts to Docs, Mail, Drive, Calendar, etc. Then navigate to your Security section of your admin panel. It should look something like mine below.
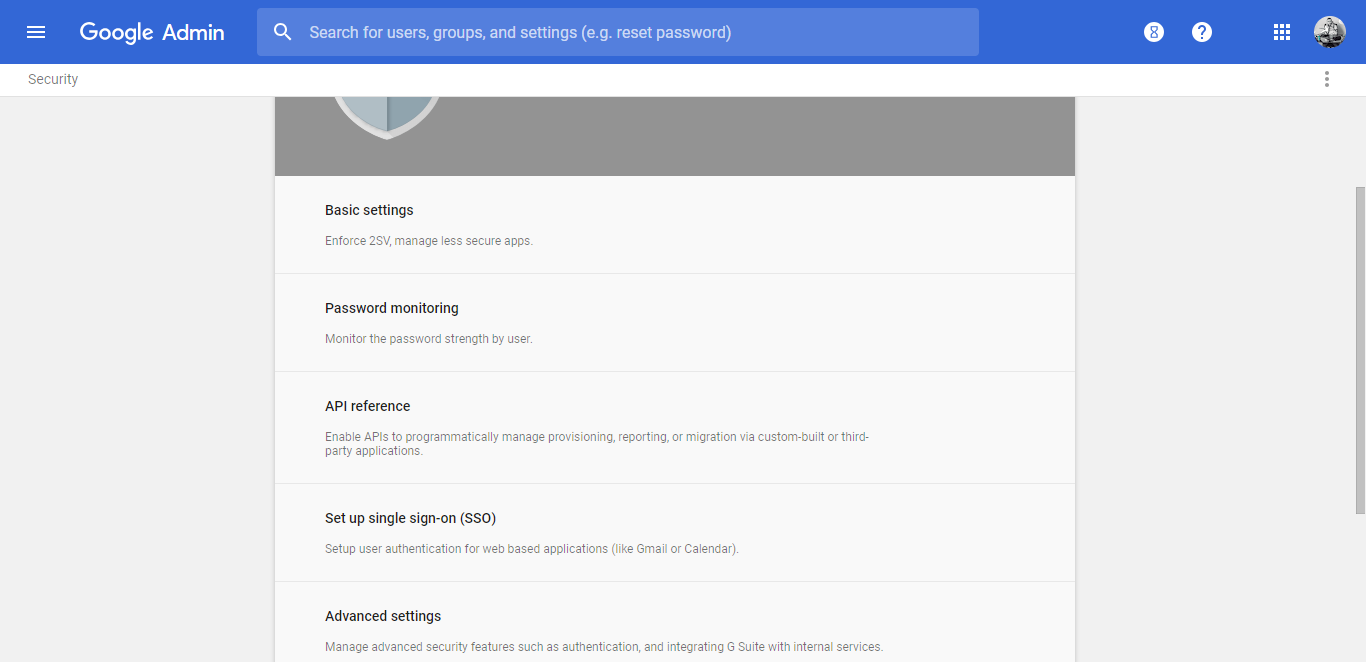 From here you can click onto Basic Settings.
From here you can click onto Basic Settings.
This will show you the option to turn on two factor authentication as an optional security measure for users to opt into.
Once you have turned this on, you will be able to enter into the advanced settings. In the advanced settings you can enforce two factor authentication on all the users of your GSuite organization.
You can either enforce it right now or you can schedule the enforcement to begin at a future date, giving you time to inform your users about what it is, why it is important, and how it works.
There is another section on the advanced settings where you can allow users to have “trusted devices”. This would mean users would not need to use two factor authentication every time they log in, provided they are on a device they have declared to be safe.
Trusted devices make the experience easier for the user by reducing friction, but may not be ideal if your workspace involves the use of shared computers or other security worries.
How to log into your Google account with two factor authentication
From your Google account, whether in your GMail or Drive, you can click on your icon in the top right hand corner and be given the option to go into the My Account screen. You can see how it looks in the image below.
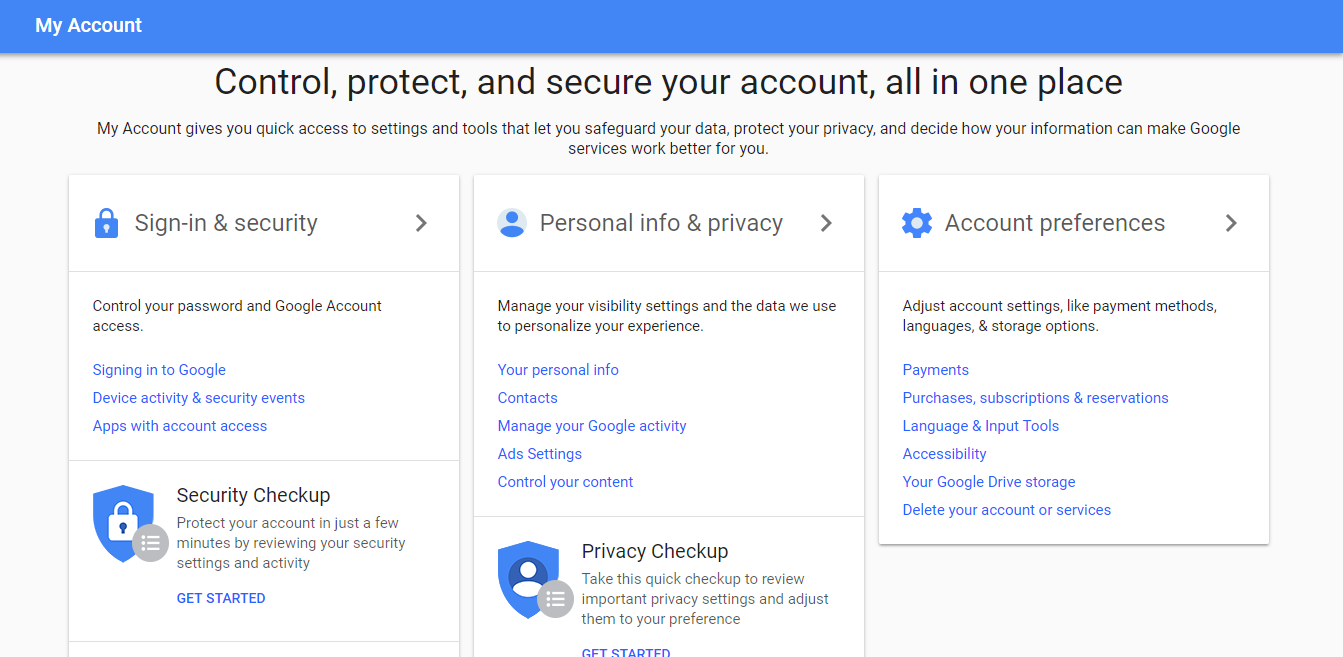 If you click on Sign-in & security you can manage how you access your account in future.
If you click on Sign-in & security you can manage how you access your account in future.
This will have a section where it shows you whether two factor authentication is turned on or off. To turn it on, click on the little arrow and it should send you to a two factor authentication wizard, shown below.
 This will walk you through the process of adding a security failsafe.
This will walk you through the process of adding a security failsafe.
Google will text you a code to verify your account. Then Google will ask you if you want to turn 2FA on for your account.
Now you’ve set up two factor authentication for your account!
But wait, there’s more…
Extra security add-ons can make the experience smoother
Google offers you some extra optional steps to improve your experience of 2FA. You can see them listed in the image below.
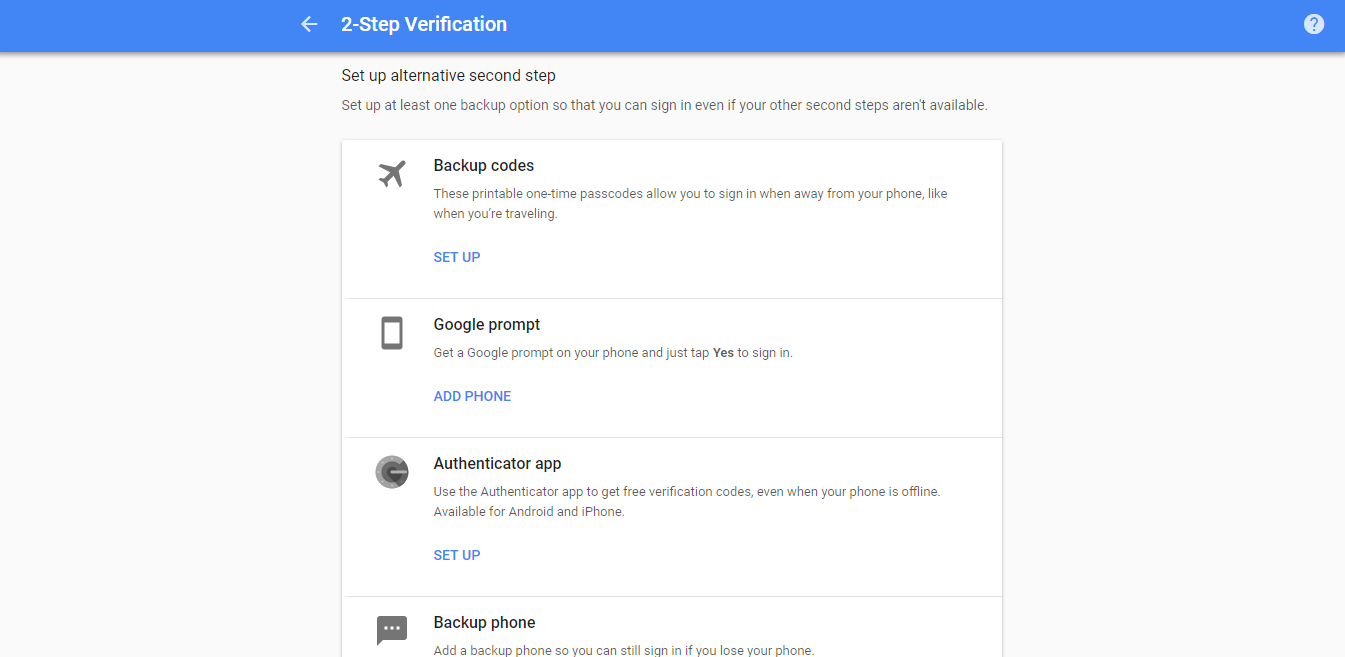 Some of these are simple. Adding a backup phone is really useful for someone like me as I often use different phones depending what country I’m in.
Some of these are simple. Adding a backup phone is really useful for someone like me as I often use different phones depending what country I’m in.
Alternatively, you can use the Google prompt option for a more streamlined experience through your mobile phone. The Authenticator app is similar, allowing you to process verification codes on your phone even when it’s offline. The section after Office365 will explain how to set up the authenticator app Authy, which I really recommend doing!
The final option is backup codes. These are one time use codes which can verify your identify if asked for a verification code.
Our recommendation is to store these codes as a note in a password management system like LastPass or 1Password. This way, you only have to remember one set of login details to retain them. Either that, or store the backup codes securely offline.
How to setup two factor authentication for Office365

Much like the GSuite process, setting up two factor authentication in Office365 is a simple process:
- Open the Office365 admin center.
- Go to Users and then to Active Users.
- Click on the More tab to show a dropdown selection of options.
- Select the option Setup Azure multi-factor auth.
- Select all the users you want to provide 2FA to.
- On the Quick Steps menu choose Enable.
Consult the Office365 help article here for more details and troubleshooting options for if your organization uses older offline software, such as old versions of Outlook.
How to setup a two factor authentication login for Office365
The process is essentially the same with Microsoft as the one for Google, but with an extra step. Provided your admin has enabled two factor authentication, then the user should be presented with a new screen after login. This will act as a prompt to guide you through setting up 2FA.
- Log in to Office365 like normal.
- When the on-screen prompt appears click Set it up now.
- Select your authentication method and click Next.
- You will then be provided with an App Password. This is the password to use for your offline tools like Outlook.
- Then the process is finished and the next time you come to login you will be sent a verification code by the delivery method you have chosen.
If you have any problems, you can consult the Microsoft Help article to troubleshoot.
How to set up Authy to manage your two factor authentication
Authy is a mobile app which acts as a keyring for all your accounts you choose to connect with it.
Authy holds the token which lets Google, Microsoft, Slack, or whomever, know that you are you.
This creates a simple and streamlined experience where you’re able to manage all your 2FA codes in one place.
You can download Authy from one of these links:
I’ll be using Authy for iOS as I guide you through the process.
Once you’ve downloaded the app, it will prompt you to enter your phone number, as you’ll see below:
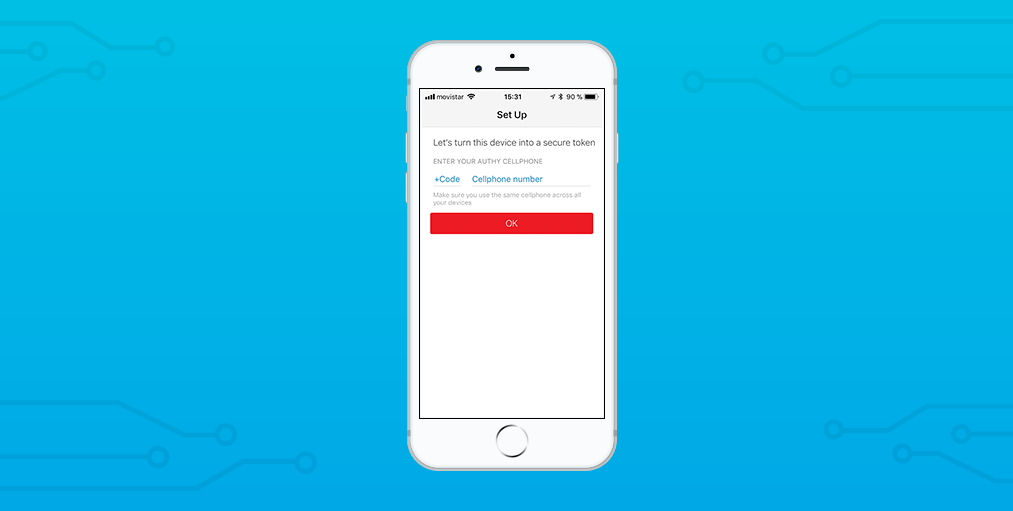 Then you’ll be asked to enter an email address. As I’m using Authy for all my professional accounts, I used my work email.
Then you’ll be asked to enter an email address. As I’m using Authy for all my professional accounts, I used my work email.
Once this information has been inputted, Authy will send you a text message. The text message will contain a code and a link. Either enter the code directly into Authy or click the link. Both perform the same job.
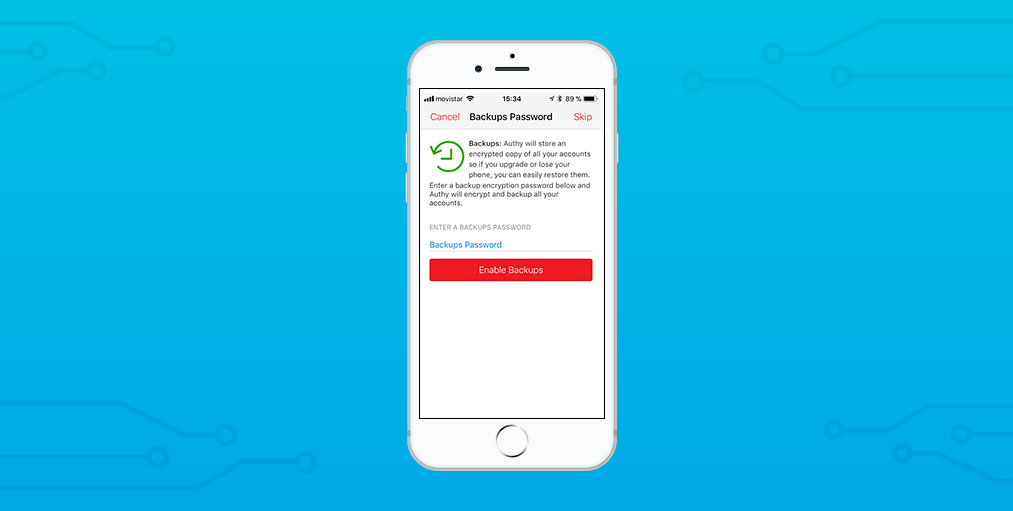
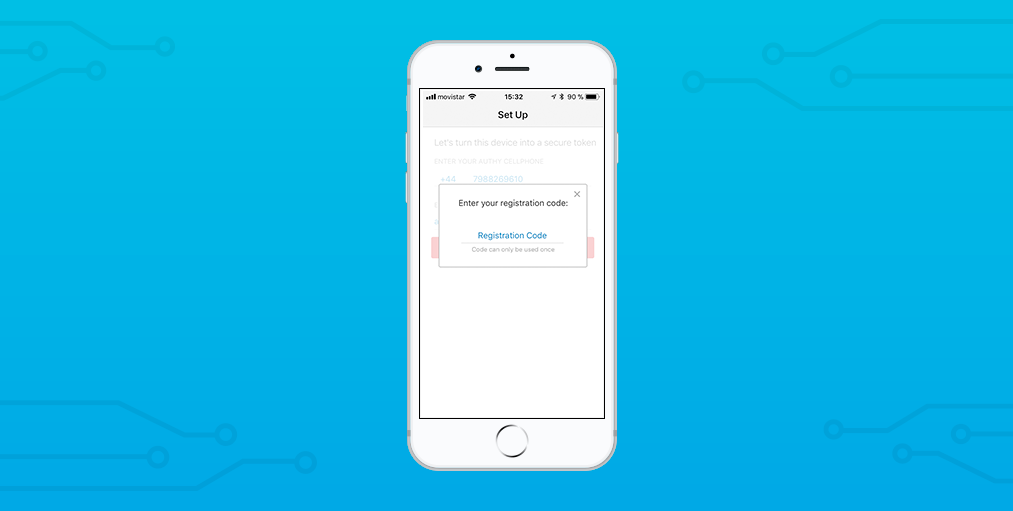 Now you’ll be prompted to create a new Authy account and to enter a backup password.
Now you’ll be prompted to create a new Authy account and to enter a backup password.
I recommend you save this password in your password manager for safe keeping.
 You’re all set up.
You’re all set up.
Your Authy account is ready to use.
As an extra little bonus, I’ll show you how I connected Authy with my Slack account.
First, tap to add a new Authy account:
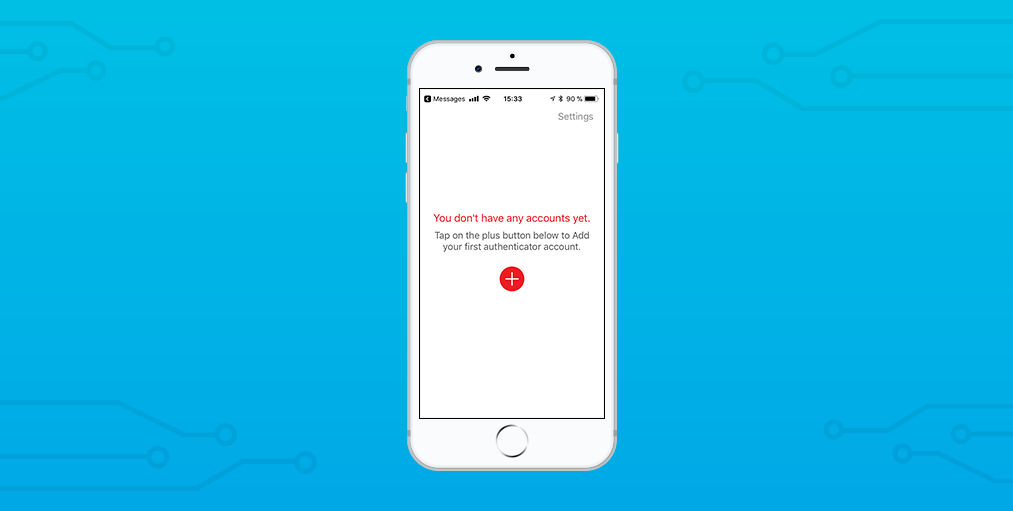 Tapping that little plus button will allow you to choose between scanning a QR code or entering a code from another service.
Tapping that little plus button will allow you to choose between scanning a QR code or entering a code from another service.
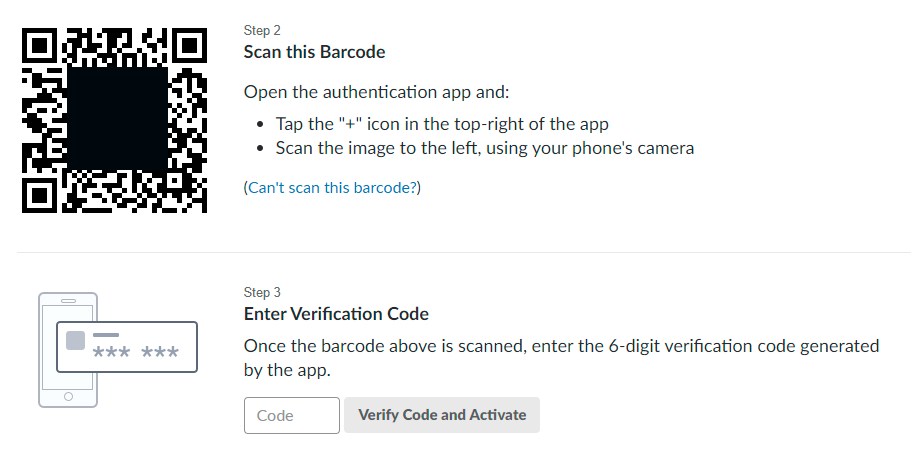
If I go into my Slack account and turn on 2FA, it gives me the option to use an app to authenticate my 2FA. Slack then shows me the following screen with my QR code ready to be scanned:
 After scanning the code with my mobile, Authy checks to make sure it has the right app:
After scanning the code with my mobile, Authy checks to make sure it has the right app:
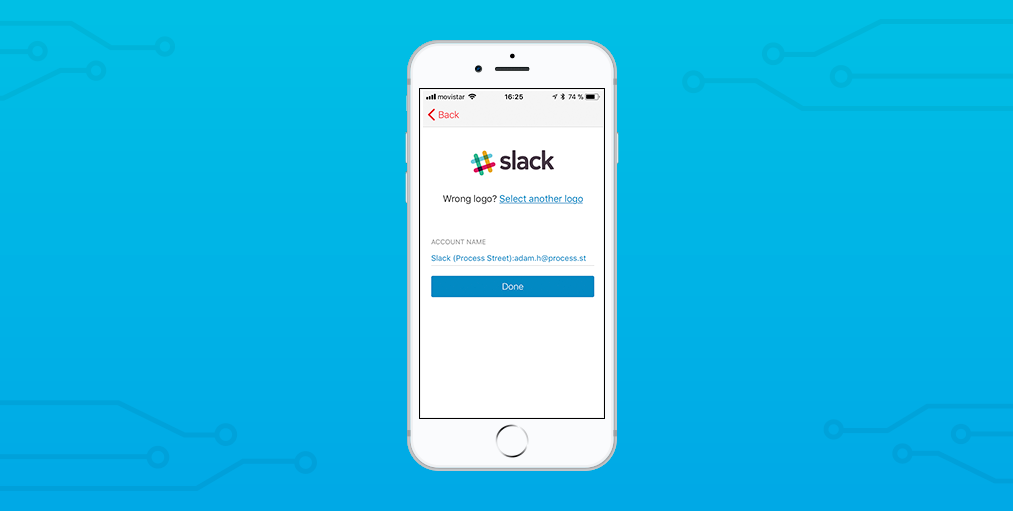 I simply tap Done and enter the code Authy gives me into the account screen in Slack.
I simply tap Done and enter the code Authy gives me into the account screen in Slack.
Now the two apps are synced and I’m ready to roll.
How to enable two factor authentication with Authy, Google, and Slack
This template has been designed to guide a user through setting up 2FA with Google and Slack using Authy.
Just click I want this for my business in the top left corner and it will be added to your Process Street account!
Implement two factor authentication in your team and boost your security
Improving security is a journey.
It isn’t a one step thing. You need to set the systems up and get people used to following the right processes to keep those systems secure.
As technology advances, these means of access may change and evolve, automating parts.
As long as security is at the forefront of your mind and you have processes in place, your company will be in a great position to provide the safety and security which your users need.
Have you implemented two factor security in your organization? Let us know in the comments below!





