
Organizations exist to create value for their stakeholders. By setting objectives, developing strategies, following through and continuously improving processes, value is created.
That’s the ideal situation, at least. In reality, it’s not always as simple as making a plan and sticking to it. There’s always the risk that certain events could affect the success of these plans.
It’s the job of management to make adequate preparations to ensure that systems are in place to continue hitting objectives, even when the beast of unforeseen circumstance rears its head.
Enterprise risk management (ERM) is a direct solution to these kinds of uncertainties, allowing management to oversee the continual creation of value on a complete, integrated, organization-wide level.
By utilizing an effective ERM system, you can rest assured that the organization will see a consistently high success rate in terms of hitting objectives and KPIs.
Stakeholders of all kinds, from customers, suppliers, government and regulatory bodies are all increasingly interested in how businesses are implementing ERM. A well-implemented ERM system could set the foundation for many high-quality, long-term client relationships.
Equally, not having a proper system for enterprise risk management could mean your business is perceived as less competent, and could even result in loss of clients and damage to brand image.
In this post, I’ll discuss:
- Introduction to and basics of enterprise risk management
- Benefits of a well-implemented ERM system
- Core ideas of ERM
- Examples of different ERM approaches
- The enterprise risk management process
- Implementing ERM
- Automating ERM
To begin with, I’ll start by breaking down the full scope of an ERM system, and some basic definitions.
What is enterprise risk management (ERM)?
Enterprise risk management, often shortened to ERM, is a type of process management strategy that seeks to identify, understand, and prepare for the kinds of dangers, hazards, and other potential deviations from standard operating procedures that could be perceived as risks.
“The culture, capabilities, and practices, integrated with strategy-setting and performance, that organizations rely on to manage risk in creating, preserving, and realizing value.” – The Committee of Sponsoring Organizations of the Treadway Commission (COSO), from Enterprise Risk Management – Integrating with Strategy and Performance
As well as identifying risks, the practice of enterprise risk management also involves making preparations for dealing with these risks and deciding prioritization over multiple active or potential risks.
Plans, policies, and procedures for risk management should be made available as widely as possible; shareholders, stakeholders, investors, and other relevant interested parties should all have clear, direct access as part of documented information or regular reports.
ERM is utilized in all industries, from construction, finance, aviation, healthcare, energy, and marketing.
The International Standardization Organization (ISO) defines risk management as:
“coordinated activities to direct and control an organization with regard to risk … [a] systematic application of policies, procedures and practices to the activities of communicating and consulting, establishing the context and assessing, treating, monitoring, reviewing, recording and reporting risk.” – ISO 31000 – Risk Management Guidelines
Risk management is not a new concept; historically, companies would manage risk with insurance policies. Liability, malpractice, loss or injury, property insurance, natural disasters – different policies to “manage” different risks relating to different business activities.
In recent years, as standards for risk management have become more established and seen widespread adoption, risk management has become more akin to a business process management framework. That is to say, ERM systems will typically focus more on control of internal processes, using principles of continuous improvement, internal audits, compliance with standards – seeking to minimize controlled risk as much as possible, as well as setting up preventative measures for risks and hazards outside the scope of control of business processes.
Let’s look at some of the benefits of successfully implementing an ERM program.
Benefits of a well-implemented ERM program
It’s important that relevant interested parties understand the rationale for implementing ERM; that way the whole organization can be aligned towards a singular common objective, and adoption will be streamlined. Making sure everyone understands the value and reasoning behind adopting an ERM system is one of the first steps to successful implementation.
Let’s look at some recent studies.
A 2008 Deloitte survey asked a group of participants to identify the benefits of ERM in terms of how they felt benefits had already been experienced, and how they thought benefits would manifest in the future.
Deloitte survey results: ERM benefits experienced
- 34%: ERM created a risk-aware culture.
- 29%: We can now identify and manage cross-enterprise risks.
- 26%: ERM provided integrated management reporting.
- 26%: ERM enabled a focus on the most important risks.
- 25%: ERM reduced vulnerability to adverse events
- 25%: ERM enhanced risk response decisions.
Deloitte survey results: ERM benefits expected in the future
- 49%: Ability to link growth, risk, and return.
- 44%: Ability to align risk appetite and strategy.
- 44%: Ability to provide integrated responses to multiple risks.
- 42%: Help to minimize operational surprises and losses.
- 39%: Help to seize opportunities.
When devising initiatives for ERM implementation, companies should try not to focus too much on the negatives; risk management can and should be seen as an opportunity for process improvement.
Traditional approaches to risk management tend to focus heavily on the down-sides, such as how much money could be lost, the extent of damage done in a cyber-attack.
To focus on the potential for process improvement means utilizing risk management as an opportunity to gain competitive advantages.
It also means processes can be improved and optimized, so that the end result is not only (for example) circumvention of potential disaster down the road, but near-term benefits and immediate benefits as a result of process changes.
Enterprise risk management: Core areas
Today, risk management has taken on a broader role, covering four core areas:
1. Hazard risk management
To assess hazards, risk managers follow these five steps:
- Identify exposures to risk
- Assess the frequency and severity of these exposures
- Identify alternative approaches (including process improvements)
- Choose an alternative and implement it
- Monitor the implementation and adjust as needed
This process is focused on both preventative and crisis risk management.
While not specifically relating to any one framework of ERM, the example below clearly illustrates the relationship between risk, hazard, and exposure:
2. Internal control
This is another way of saying the meta-processes that companies use to make sure internal processes are being followed.
Internal control processes are also used to improve process efficiency in areas such as reporting, conformity, and general process effectiveness.
Larger organizations, especially those in highly regulated industries, will often have elaborate and expansive systems of internal control.
3. Internal audits
Simply put, internal audits are used to make sure internal controls are working properly. This is different to risk management – it’s another meta-level process that looks instead at the cost, efficiency, and effectiveness of the ERM processes.
Internal audits are concerned with how the risks are actually being managed in practice, and how this evidentiality sits in-line with the documented policies and procedures of the ERM.
Teams of internal auditors will look at operating activities, consistency, and compliance. Results of the audit including weaknesses and recommendations are typically given in the form of an audit report.
4. Regulatory compliance
Certain rules and regulations must be followed by companies; this area of enterprise risk management concerns efforts to make sure these requirements are met.
For example, government bodies may issue requirements for site safety, environmental policy, social responsibility, or financial reporting.
Companies will typically have a specialized compliance unit or officer who interprets these requirements, giving advice, training, and recommendations for conformance.
Examples of ERM approaches
Over the years, various frameworks for ERM have been established. Each of them describes a different approach for the identification, analysis, response, and general management of risks and opportunities.
Here are a few of the most prominent ERM approaches:
ISO 31000
ISO 31000 refers to a family of standards for risk management, defined by The International Organization for Standardization.
As well as the wider family of standards, ISO 31000 also refers to a specific standard within that family. ISO 31000:2018 is the most recent version at the time of writing.
ISO 31000:2018 for risk management provides a set of guidelines for organizations to manage risk. It is not a set of requirements, and as such cannot be certified to, unlike other ISO standards like ISO 9001.
Other standards in the family include IEC/FDIS 31010 – Risk Assessment Techniques, which provides guidance on specific techniques for risk management.
CAS
The Casualty Actuary Society (CAS) is a society of professionals trained in the discipline of actuarial science, specializing in property and casualty insurance.
In 2003, the society’s Enterprise Risk Management Committee defined ERM using two concepts: risk type, and risk management processes.
Of ERM they said the following:
“…the discipline by which an organization in any industry assesses, controls, exploits, finances, and monitors risks from all sources for the purpose of increasing the organization’s short- and long-term value to its stakeholders.” – CAS ERM Committee, from Overview of Enterprise Risk Management
Examples of risk type include:
- Hazards: e.g. natural disasters and property damage
- Financial risks: e.g. asset, securities, or fiat currency risk
- Strategic risks: e.g. business competition and trends
- Operational risks: e.g. customer satisfaction, brand integrity, reputation, product faults and failure
Risk management process:
- Establish context: internal and external scope of the organization, and the scope of the ERM system
- Identify risks: As they relate to the organization’s objectives; these should be well-documented and include the corresponding potential for gaining competitive advantage as a result of process improvement
- Analyze severity risks: For each of the risks identified, assess (and if possible, quantify) the severity of each risk
- Integrate risks: Based on the results of previous risk analysis, aggregate all risk distributions and align the analysis with the determined impact on KPIs
- Prioritizing risks: Determine a ranked order of prioritization for each of the risks identified
- Risk management strategies: This involves strategies for resolving and exploiting risks identified
- Monitoring and reviewing results: The continuous improvement of the risk management process by way of monitoring and assessment of the risk environment; basically what works and what doesn’t, and figuring out how to improve the process
COSO
COSO is a joint US initiative established in 1985 to prevent corporate fraud. Their recently published Enterprise Risk Management: Integrating with Strategy and Performance (2017 Edition), states:
“Enterprise risk management is not a function or department. It is the culture, capabilities, and practices that organizations integrate with strategy-setting and apply when they carry out that strategy, with a purpose of managing risk in creating, preserving, and realizing value.” – Enterprise Risk Management: Integrating with Strategy and Performance
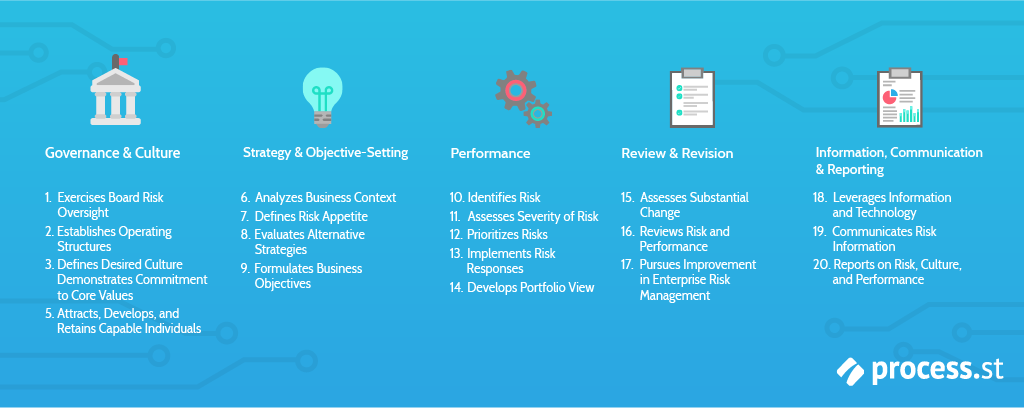
The same publication goes on to organize the framework into the following five components:

1. Governance and culture:
Enterprise risk management cannot succeed unless the organization seeks to fully integrate it within the culture of their workplace.
This pertains to the ethics behind worker responsibilities, codes of conduct, and the proper comprehension of risks, as well as all associated management programs and solutions.
2. Strategy and objective-setting:
A fundamental part of ERM is making sure the risk management strategies align with core objectives and broader business strategies.
Business objectives are the basis for planning and implementing strategies, while simultaneously serving as a launch-pad for identifying, assessing, and responding to risks.
3. Performance:
Assessing how certain risks will impact the performance of key processes is important for risk prioritization.
In this context, risks are prioritized in order of their severity.
Following this, risk responses are selected based on an assessment of the potential for risk that has been identified. Results of this part of the process are typically reported to key stakeholders.
4. Review and revision:
By reviewing the performance of risk management processes, organizations can determine how well the ERM program is working, including whether or not changes are needed.
5. Information, communication, and reporting:
ERM is not a single checklist or a fixed set of steps; it is an ongoing process of collecting and assessing information from internal and external sources, across all parts of an organization.
The five components above are supported by an additional set of principles. These principles are wide-ranging, covering everything from corporate leadership of the ERM program to risk monitoring methods.
Each of the principles are short and succinct; here they are, as they appear in Enterprise Risk Management: Integrating with Strategy and Performance (2017 Edition):

Organizations can use these principles as a clear reference point for contextualizing and evidencing their efforts to understand and strive for an enterprise risk management program that is firmly aligned with its strategy and business objectives.
Enterprise risk management process
The process (or cycle) of enterprise risk management has five main parts:
- Objectives
- Identification
- Assessment
- Response
- Monitoring
1. Setting objectives and aligning ERM with business strategy
At the heart of the COSO ERM framework is the idea of using enterprise risk management to succeed in realizing its business objectives.
ERM alone will not realize business objectives; rather the fruits of the ERM program are vital for strategizing to achieve and exceed those business objectives.
Using an ERM framework helps to ensure that a business is able to align objectives with mission, vision, and core values.
2. Identification and documentation of risks
Risks are to be considered as anything that could potentially impact successful achievement of business goals. All risks should be clearly identified and well-documented.
That includes everything from larger, more significant risks, all the way down to smaller risks on the level of individual projects or processes.
In order to successfully identify risks, a clearly defined process is required to systematically assess each area of operation.
3. Assessment of documented risks
Simply identifying risks is not enough; impact of the risk should be understood, as well as probability, within an estimated time-frame.
Once significant risks have been adequately documented, the next task is to assess them in terms of their likelihood and estimated significance.
Sometimes, it’s difficult or impossible to accurately predict the probability or time-frame of certain risks, for example natural disasters. Nonetheless, this exercise should be performed to the best of the organization’s ability, and across all levels.
This task is especially important to make sure that all documented risks have substantial credibility. Off-the-cuff suggestions recorded in group brainstorming sessions might have sounded good at the time, but they need to stand up to further scrutiny. Qualitative and predictive analysis will help sort the risks by order of significance.
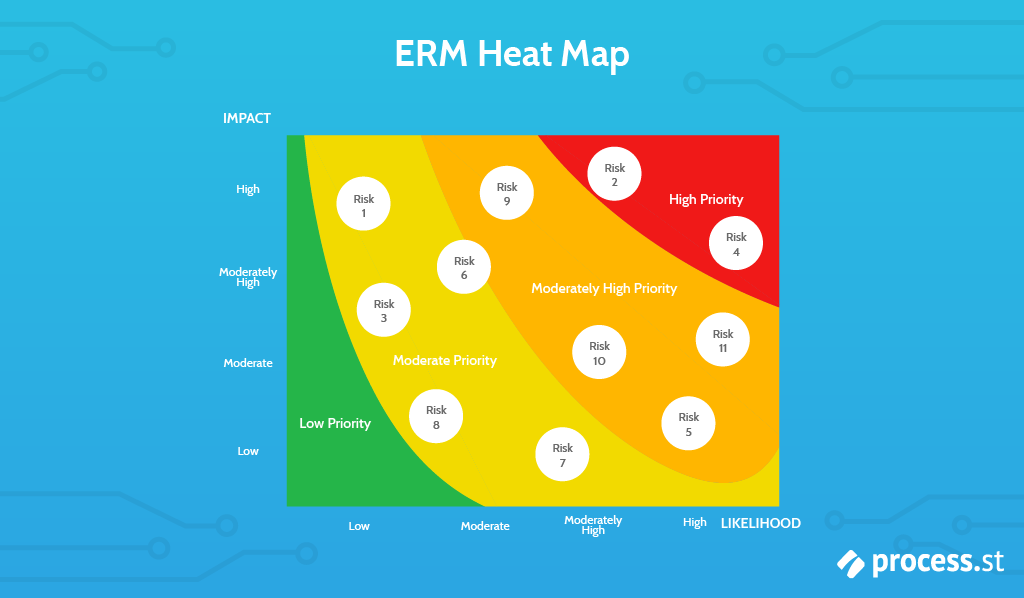
Various methods exist for assessment of documented risks, from simple qualitative approaches like the prioritization matrix, to more in-depth mathematical models.
The point of this task is to help management determine which risks deserve the most immediate attention.
Another option is to create a heat map of risk significance. The goal of a heat map is to support the results of a risk assessment with an illustration to supplement an active dialogue on how the results compare with an organization’s current risk appetite and determine urgent solutions that might need implementing.
Below is a simplified example of a post-risk prioritization review heat map which excludes lower priority risks, where impact is quantitative (e.g. financial losses) and likelihood is probability of occurrence within a given time period. The graph is adapted from AICPA’s Enterprise Risk Management: Guidance for Practical Implementation and Assessment (2018):
4. Risk response
Risk response is intended to figure out how to respond to the high-priority risks.
The responsibility falls to management to carefully review the probabilities and estimated impacts of each risk, and to consider all associated costs and benefits in developing an appropriate risk response strategy.
Risk response falls into four categories of its own:
Avoidance
As the name clearly suggests, this type of risk response involves simply “walking away” from the risk.
For example, a company might decide to relocate based on risks resulting from certain geo-political tension, or completely abandoning a product or service that is proving to be particularly risky.
Often it will be too late to avoid risks, because the damage has been done and the costs incurred.
That’s why preventative measures and adequate analysis of potential risks are so important – to keep the avoidance response on the table.
Reduction
Often, risks can be reduced in a number of different ways.
Diversifying a product line may reduce the risk that changing trends or seasonal buying poses, employing multiple stop-gaps for fault tolerance like offline backups and multiple operations centers will reduce the risk posed by natural disasters, automating certain tasks in a process will reduce the risk of human error, and so on.
Simple tweaks to standard operating procedures, even seemingly mundane changes like making sure employees are properly informed on company policies can sometimes result in significant reduction of risk.
Sharing
Risk “sharing” is the principle of purchasing insurance to hedge or offset their risks.
To use a financial example, the concept of short calls and long puts allow investors to hedge their bets on price movements.
Joint venture agreements can also mean businesses share potential risks and rewards.
Basically, risk sharing is the idea of having a portion of the risk offloaded onto another party with the understanding that you’re substituting the perceived “value” of that risk for a more tangible monetary cost.
Acceptance
To accept a risk is to take no action.
Rather than buying an insurance policy, a business may decide to “self-insure”. This might take the form of putting aside resources to deal with certain risks, should they manifest.
5. Risk monitoring
Identifying risks isn’t something that’s done once – like continuous improvement, it’s an ongoing process.
The context in which certain risks are identified is constantly changing, and as such risks need to be monitored to continually determine the significance they represent.
Sometimes, changing circumstances may lead to the risk becoming even greater. A clear example of this is geopolitical unrest. Organizations need proper systems in place to monitor and respond to changes in circumstances and adequately determine if identified risks still pose a threat.
Case of the Russian frozen chickens: A lesson in enterprise risk management
To supplement your understanding of enterprise risk management, I have adapted a case from John J Hampton’s Fundamentals of Enterprise Risk Management: How Top Companies Assess Risk, Manage Exposure, and Seize Opportunity.
The case examines four aspects of risk identified in pursuit of a risk opportunity associated with the export of a cargo of frozen chickens from Virginia and North Carolina to St. Petersburg, Russia.
The company planned to load a number of 60-80 pound boxes on pallets for an ocean voyage. Except, the port of St. Petersburg had no shoreside refrigeration to allow quick unloading of an expensive reefer vessel.
Expropriation risk
If the ship wasted too long docked in St Petersburg waiting for containers to offload the shipment, it would incur significant fees for delayed operations.
One solution would be to build a warehouse, but the risk manager identified an expropriation risk.
A case from the mid-1990s was cited: a European-invested Hotel in St. Petersburg incurred hefty fines after the Russian government learned it was using a foreign bank account to handle dollar transactions. The result was the expropriation of the hotel premises by the Russian government.
While the risk manager knew she could obtain reimbursement insurance from a U.S. government agency, the identified expropriation risk didn’t seem to be the answer.
Therefore, the company opted to seek a strong Russian partner with high-level government connections and allow the partner to accept the appropriation and storage exposure.
Lesson learned: Investigate all options for risk reduction. Don’t assume that the obvious approach is the best answer!
Credit risk
So far so good; the company had a strong Russian partner. This was also bad news, as it created a credit risk.
How could the U.S. company make sure the Russian partner paid in a timely manner? It wasn’t realistic to ask for an up-front payment, neither was it reasonable to obtain a letter of credit guaranteeing future payment.
As it transpired, the Russian partner was not able to pay for the first cargo cargo until 30 days after receiving it. To deal with this problem of credit exposure, an agreement was made that the Russian partner would pay for one cargo before it received a subsequent.
This mitigated exposure to credit risk because the stream of profits from a series of cargo shipments was significantly larger than a default payment on a single cargo.
If the Russian partner didn’t pay by day 45 after receipt of a cargo, the ship carrying the next cargo would be diverted from Russia to a northern European port.
Lesson learned: Give other parties incentives to help your organization mitigate risk.
Physical security risk
Once the Russian partner accepted the chicken in St. Petersburg, the shipment was transported by rail to Moscow, Yekaterinburg, and beyond via locked refrigeration containers loaded onto flat railcars.
On the fifth journey, one of the containers was discovered to be empty when it arrived in Moscow after the three-day trip from St. Petersburg. The shipment had been stolen.
At this point, the partner was facing a physical security risk.
Two viable strategies were identified:
- Purchase insurance
- Door-to-door container placement so that the doors could not be opened if the locks were broken
The first strategy was dismissed quickly. Who would insure a cargo with an already-existing high chance of loss? Premiums would be prohibitively high.
The second strategy was chosen.
This proved effective for a time; however, the story was not over. Several journeys later, another container arrived empty.
Realizing that someone had a crane on a siding when the train stopped in the middle of the night, the Russian partner considered what else should be tried.
Finally, the problem was solved by placing a boxcar on the back of the train. The car had fitted heaters and cots, carrying guards armed with Kalashnikovs. Whenever the train stopped, the guards stepped out to protect the containers.
Lesson learned: Sometimes it’s worth sticking with a risk management strategy, tweaking and fine-tuning the solution until the problem is solved. Not everything will work out-of-the-box.
Upside of Risk
While the security situation on Russian railroads has improved significantly since the 1990s, this story also identifies the upside of risk.
Once the cargo was being protected by armed guards, the Russian partner had the opportunity to offer insurance services to third parties to protect their cargoes as well as the frozen chickens.
The loss incurred from managing the risk with the paid armed guards and rear boxcar would, in that case, be offset by the confidence that the train would experience no losses, and the additional revenue from the insurance services offered.
Lesson learned: Risk management does not end with the mitigation of risk – always look for an upside!
Manage your risks with automation
You can also investigate the potential for automating aspects of your ERM system.
Much of the implementation of an ERM system is a one-time process, but just as many if not more of the tasks involved in the continuous maintenance and improvement of an ERM system will be repetitive manual work.
For example, many repetitive tasks for review and revision of risk contexts will have to be done over and over again. Processes can be long, complex things, and the very process of carrying out an ERM implementation carries risks of its own!
For example, human error is a massive cause of process failure.
By automating these manual tasks, you are reducing the potential for human error to occur.
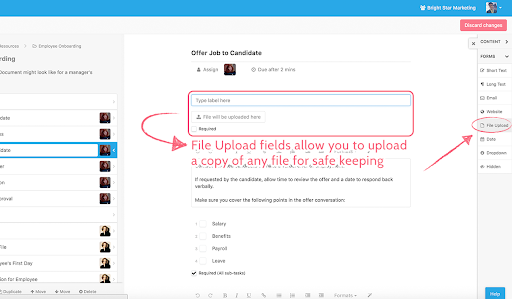
Process Street is a business process management software designed to eliminate manual work from your daily tasks.
We have a huge library of pre-made templates, all of which are free to use.
Check out this webinar for an introduction on how to use Process Street for enterprise risk management:
If you found this article useful, you might be interested in these resources:
- SWOT Analysis Template: What, How, & Why? (Free Template)
- What is FMEA? A Practical Guide to Failure Analysis (Free Checklist)
- Office Risk Assessment Checklist
- What is Quality Management? The Definitive QMS Guide (Free ISO 9001 Template)
- The Complete Guide to Business Process Management
- The Ultimate Guide to Business Process Automation
Don’t forget to sign up for a free Process Street account! It takes less than 2 minutes.
How do you approach enterprise risk management? Do you use any specific frameworks, tools, or approaches? Let us know in the comments below!







 Workflows
Workflows Forms
Forms Data Sets
Data Sets Pages
Pages Process AI
Process AI Automations
Automations Analytics
Analytics Apps
Apps Integrations
Integrations
 Property management
Property management
 Human resources
Human resources
 Customer management
Customer management
 Information technology
Information technology



Oliver Peterson
Oliver Peterson is a content writer for Process Street with an interest in systems and processes, attempting to use them as tools for taking apart problems and gaining insight into building robust, lasting solutions.