The modern workforce is, quite literally, movers and shakers.
No matter if self-bought or company-bought, employees are using mobile devices to work from while in the office, going from meeting-to-meeting, traveling cross-country to attend conferences, and even when working from home.
But for some (read: the security-minded), this is a little worrisome. With employees using personal and portable devices for work purposes, security hazards are aplenty. Theft. Security breaches. Data loss.
I needn’t go on.
It’s why 75% of CIOs view mobile security for organizations as not only a headache but a significant problem.
Though, with modern problems come modern solutions.
In this super informative post, I’ll be discussing EMM: Enterprise mobility management. It’s what every organization needs to know about, incorporate, and sustain so that its business remains security breach-free. Just read through the following sections to get acquainted with all-things EMM:
- What is EMM (enterprise mobility management)?
- BYOD and the benefits of enterprise mobility management
- Device management: The EMM best practices
- How Process Street can help your organization with EMM!
Now, let’s stop dilly-dallying and get started!
What is EMM (enterprise mobility management)?
Enterprise mobility management (also shortened in acronym form as EMM) is the processes, procedures, and technology that helps to secure mobile devices in a business context.
For instance, there could be specific software for the IT team to control devices externally, processes to ensure workers are secure while using their mobile devices, and procedures to make sure that, if the worst comes to the worst, employee and corporate data alike doesn’t find itself in the wrong hands.
The team at Citrix define EMM as:
“Enterprise mobility management (EMM) is a set of technology, processes, and policies to secure and manage the use of corporate- and employee-owned mobile devices within an organization. EMM is constantly evolving to accommodate an ever-changing set of device platforms and mobility trends in the workplace.” – Citrix, Definition of employee mobility management
All in all, it’s rather a broad term. What it boils down to, however, is keeping data and devices safe, so the organization in question doesn’t go kaput should a device get lost, stolen, or corrupted.
Now, enterprise mobility management didn’t just appear out of thin air. To truly explain what EMM is, it’s imperative to talk about BYOD – the bring-your-own-device movement.
BYOD: Bring your own device
Remember this old guy?
(The computer. Not the child, obviously.)
This was the Apple II. It was one of the world’s most loved, mass-produced computers on the market. From homes to offices across the U.S., these beastly bad boys were everywhere. For organizations in particular though, they were something of a godsend for business efficiency – even if, due to their humongous size, they were by no means portable.
Technological advancements were soon made, though. In 1981 – 4 years after the Apple II was released – chunky computers were condensed down into laptops; portable computers that could be taken anywhere.
The leaps and bounds technology made didn’t end there.
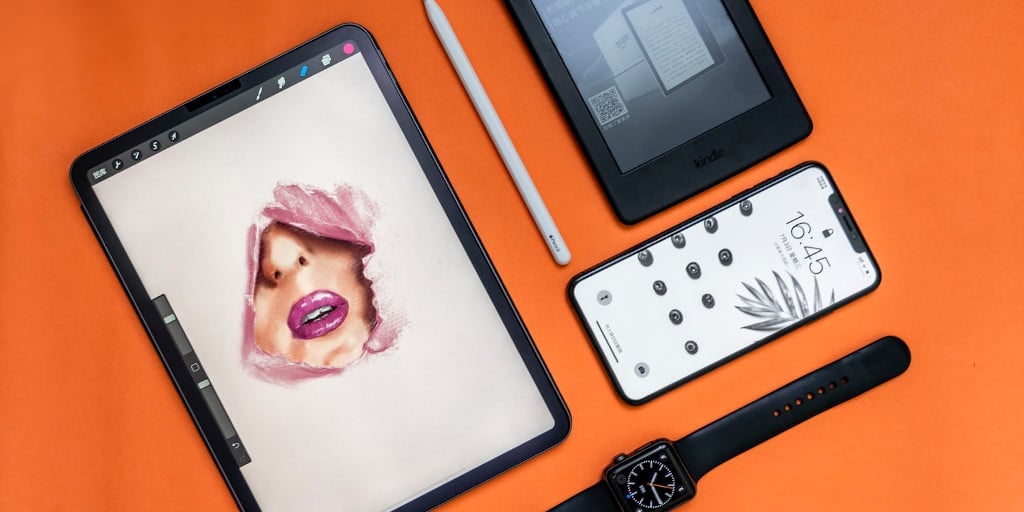
Cellphone technology advanced, too. Cellphones grew – or rather, shrank – into hand-held computers that were far more accessible, powerful, and useful than the mobile phones of olde (see video below), and even the Apple II, for that matter.
By the tail-end of the 2000s, everybody had an iPhone or a Blackberry, a Windows laptop or a MacBook. Plus, tablets started becoming the lynchpins for forward-thinking organizations, meaning tablets were becoming commonplace in the office.
Ultimately, with technology becoming affordable and portable, it meant employees were no longer tethered to the chunky computers that awaited them at their desk each morning.
Instead, employees could work from their laptops, cellphones, and tablets not only inside the office but outside of it, too.
This is when the bring-your-own-device (to work) movement truly kicked-off.
It changed things. Forever.
MDM: Mobile device management
The bring-your-own-device movement, although fantastic (more on that later!), came with a few issues.
What would happen if an employee accidentally left their device on a train? At an airport lounge? Inside the plane itself?
Similarly, what would happen if viruses made their way onto the device? If the device got corrupted?
Not to sound too doom-and-gloom, but it could destroy an organization within minutes.
That’s why mobile device management (MDM) came about to counter many of those issues.
Simply put, MDM allows the IT team at an organization to successfully manage their employees’ mobile devices. With MDM, the corporate network is guarded, mobile devices are secured, and devices have more functionality too.
But how, exactly, does it work?
The experts at SearchMobileComputing explain rather succinctly in the quote below:
“Mobile device management relies on endpoint software called an MDM agent and an MDM server that lives in a data center (either on-premises or in the cloud).
IT administrators configure policies through the MDM server’s management console, and the server then pushes those policies over the air to the MDM agent on the device. The agent applies the policies to the device by communicating with application programming interfaces (APIs) built directly into the device operating system.” – SearchMobileComputing, Mobile device management (MDM)
With MDM, the IT professionals at an organization provide their employees with a more secure experience (employees can send emails, access documents, and search the web securely via data encryption), while simultaneously having the power to wipe those devices, should mobile devices be accidentally left on that JFK flight to LHR!
To coincide with MDM, there’s also MAM…
MAM: Mobile application management
This is the last definition, I promise.
Mobile application management (MAM) provides an organization’s IT professionals with the ability to control and manage corporate applications and the data that’s stored, transferred, or transmitted via those applications.
So, to differentiate the two, MDM focuses on employees’ devices, while MAM is to do with the applications on those devices.
Still not 100% sure what the difference is?
Read this succinct paragraph written by the team at V-Soft Consulting:
“With MDM, IT is capable of wiping or locking an employee’s phone. With MAM, however, they could simply lock the user out of their corporate e-mail without the user worrying about his personal data becoming inaccessible.” – V-Soft Consulting, BYOD in the Workplace: The Difference Between MDM and MAM
MAM, then, goes slightly deeper than MDM, because it’s focusing on the applications and software on the device, rather than just the hardware!
Back to EMM: Enterprise mobility management!
So, how does EMM figure into all of this?
MAM + MDM = EMM? Or does EMM + MAM = MDM? What about MAM + EMM = MDM?
A lot of ground has been covered in the last few sections; don’t worry if you’re a little unsure of how our starting point – EMM – relates to MDM and MAM.
As I said earlier, Enterprise mobile management (EMM) is the processes, procedures, and technology that helps to secure mobile devices in a business context. EMM is the term for overall enterprise mobility management, and it subsumes both MDM and MAM.
Now those important definitions have been covered, let’s focus on the big picture and look at the benefits of enterprise mobility management. (Believe me, there’s a bucket load of ’em.)
BYOD and the benefits of enterprise mobility management
It’s safe to say that our interconnected, mobile world has well and truly disrupted how organizations operate – no matter if they’re office-based or working as a virtual team.
That’s why, before getting into the specific benefits related to enterprise mobility management, it’s important to acknowledge the benefits that bring-your-own-device culture has brought to the table.
After all, without the change BYOD brought, there would be no EMM in the first place!
The benefits of BYOD

- Increased productivity.
- Acknowledged as a perk for employees.
- Lowered company spend.
- Work can be completed at any time, any place.
There’s nothing worse than going back-and-forth between different devices. Take me as an example. I’m so used to my own laptop’s keyboard, trying to type on another keyboard is like learning how to type all over again. It directly slows down the blog writing process, as I’m having to consciously think about the placement of my hands in relation to the keyboard. But by using a familiar device all the time, it’s the holy grail of productivity: I can punch out posts without thinking about the act of typing. Imagine how useful it is then for employees to bring their own phones and tablets to work, too!
Like me, there are thousands of others who believe that sticking to one device – be it company-bought or self-bought – is a perk (because it is!). No matter if that’s because they prefer working with just one device or due to the flexibility that BYOD entails, BYOD culture for many is an attractive quality, not a deterrent.
Speaking of perks, not having to shell out on extra devices means organizations can lower their spend and save money!
Even if an organization is primarily office-based, not all work is done from inside the office itself. Employees are checking their emails before jetting-off for crucial meetings, finishing up projects at home over the weekends, or as mentioned earlier, knuckling-down during the morning commute. If an organization retains its BYOD culture, employees can work wherever, whenever!
Now, pros are never without their cons – BYOD is no exception.
The aforementioned negatives – such as losing devices and having data stolen – are exactly why EMM became integral for big and small organizations alike; to keep potential security threats at bay.
But what are the distinct, specific pros of using EMM to counter the cons of BYOD?
Let’s take a look.
The benefits of EMM

- Protects your employees’ data.
- Protects your organization’s data.
- Wipe and erase integral data.
- Services different kinds of devices.
- Helps with compliance.
- Provides peace of mind. ✌️
No matter if an employee is working in the office or on the road, there are (roughly) a million and one ways your employees’ data can be compromised. EMM keeps your workforce’s data exactly where it should be, and out of the hands of nefarious people or organizations.
Just as you don’t want employee data getting into the wrong hands, neither do you want corporate data to be used by any organization other than your own. The security measures that EMM solutions provide (device enrollment, device authentication, app/website blacklisting and whitelisting, data wiping) makes sure that data is secure. Always.
Data wiping and erasing has been mentioned a couple of times already in this post, and there’s a good reason for that. It’s one of the most prominent, sought-after features from an EMM solution, and helps organizations tremendously. Due to mobile devices being, well, mobile, it’s often the case that devices get lost. However, if they do, the integral personal and company data on those devices can be erased easily.
EMM solutions don’t only cover one particular brand or operating system – they go across them all. So, no matter if your organization is divided into both Windows 10 (Bonus: Check out these Windows 10 tips!) and Mac users and Android and iOS lovers, everybody is covered.
From HIPAA to GDPR, you’re required by law to ensure that client and customer data is kept safe; end-to-end infrastructure helps with this so that your organization stays compliant at all times.
Ahh. What’s better than knowing that your employees are using devices safely and securely, and that if something should happen (i.e. a device goes walkabout, never to be seen again), it isn’t the end of the world? An EMM solution provides overall peace of mind.
Fantastic pros, huh?
Everybody else thinks so, too.
A survey conducted by Forrester Research shows that 77% of telecom decision-makers want to expand on their EMM systems.
Similarly, studies from 451 Research show that EMM global revenues are forecast to grow by 25% through 2021, upping its total revenue to a whopping $16.69 billion.
Want to introduce your organization to EMM?
After reading through that solid list of pros, I don’t blame you.
But before I give you the green-light to implement EMM in your organization, there are some best practices to read, acknowledge, and understand in the section below. ⬇️
Device management: The EMM best practices

Introducing new business systems and business software – and an EMM solution in particular – to your organization can go either way.
On one side of the coin, it can dramatically streamline your organization’s mobile security, help protect essential information, and create peace of mind for all involved; the organization’s IT team, all employees, and the board of directors.
On the flip side, it can not only be confusing for your colleagues in IT to grapple with, but it can also be hard for employees to understand any new policies and procedures that come with enterprise mobility management – especially if those policies and procedures aren’t well-considered.
This may be the point where you’re thinking “How do I ensure I introduce EMM properly, and I don’t confuse my team or the rest of the organization?”
Dear reader, everything you need to know about understanding, implementing, and sustaining EMM is outlined below.
Follow these best practices and you’re set for success.
Understand your organization’s needs
First thing’s first: It’s pivotal to understand your organization’s own needs.
Why?
Because there are no hard-and-fast rules for how an organization should undergo its enterprise mobility management. What works for one organization may not work for another.
For example, one organization might only use the EMM solution’s wipe-device feature for its enterprise mobility management, while another might want to use EMM tools to their full capabilities.
Ergo: It differs on a case-by-case basis.
By understanding what it is your organization needs, you can find an EMM solution that fits those requirements.
To give you a head start, ask yourself the 5 following questions provided by Solutions Review from their article 5 Questions to Ask When Evaluating EMM Solutions:
- What management solutions do I need in my EMM suite?
- Can I just upgrade my MDM solution?
- What operating systems does an EMM solution support?
- How does the EMM solution help me maintain security?
- Does my enterprise want a SaaS or on-premise deployment?
Research different EMM solutions
Considering the sheer number of EMM solutions on the digital marketplace, you’ve got your work cut out for you.
But do not fret.
It can be made a far easier endeavor if you’re using a decision-making framework to not only speed up the process, but also to make the best decision possible.
In my post DECIDE: A Decision Making Process for Intelligent Decisions, I discuss DECIDE – an intelligent framework to help people make intelligent decisions, no matter the conundrum at hand.
I specifically mention how useful it is for choosing software here. Use the easy, 6-step framework and process to help you whittle your software choices down to the final contender.
It’ll save you time, effort, and a whole lot of stress.
Align policies: Realistic use-cases
Once you’ve made a decision regarding which EMM solution to use (see, that wasn’t so hard with help from DECIDE, was it?), it’s time to create EMM-orientated policies.
But what are these “policies”, I hear you ask?
As Samsung, who created the Knox EMM solution, says:
“Policies are sets of rules, which allow or disallow device functions (for example, disable device screenshots). Policies are also used to configure settings such as Email accounts and VPN.” – Samsung, Knox Premium Getting Started guide
Essentially, policies are the rules you set for how employees use their devices.
With this in mind, you’ll want to make sure the set policies don’t create a bottleneck by blocking your employees’ abilities to do work and complete tasks with their devices. But at the same time, you want to set policies that protect them and the data on those devices.
There’s a middle ground; align those policies to that middle ground.
Align policies: Applicable laws ⚖️
The next policy-level step is to ensure whatever policies are created are law-abiding.
As mentioned earlier, data-related acts such as HIPAA and GDPR will impact your organization’s enterprise mobility management.
Before informing your employees of the product, why it’s being introduced, how to use it, and the policies involved, double-check the policies do actually align with the applicable laws in your business’ location.
Continually review how your organization goes about EMM
Similar to how employees are given regular performance appraisals and reviews, there should be frequent reviews of your organization’s enterprise mobility management.
This is to confirm the EMM solution is working, being used properly by employees, and if any improvements could be made regarding how your organization undergoes EMM – be it using a different tool, revising certain policies, or how you introduce new employees to those EMM-based policies.
Don’t let unnecessary security issues slip through the cracks. Review, review, review.
(And review again.)
Use Process Street alongside your EMM solution!
As with many best-practice lists, I’ve saved the most useful recommendation until last.
In addition to your new EMM solution, use Process Street to help facilitate, streamline, and better your organization’s overall enterprise mobility management.
Not heard of Process Street before?
Just as BYOD changed how successful businesses operate forever, Process Street will change how your business works forever as well.
How Process Street can help your organization with EMM!
Process Street is superpowered checklists.
With our state-of-the-art BPM software, your organization can document workflows, business processes, and integral procedures via templates.
Then, whenever somebody needs to complete a process to a high standard, all they need to do is launch a checklist. The checklist will provide them with everything they must know to do the job to an A+ standard.
The beauty of Process Street is that it can be used to create basic checklists and intelligent, superpowered checklists alike.
Workflow features such as stop tasks, conditional logic, task permissions, dynamic due dates, role assignments, and approvals mean your checklists can be as powerful and as simplified as you want.
Check out the webinar below, conducted by our head of customer success Blake Bailey, to understand some of these aforementioned features in greater detail.
If you’re wondering “How, exactly, can Process Street help with EMM?”, I hear you.
You can create a process for everything with Process Street. But for EMM specifically, you can use our nifty checklist app to:
- Undergo regular EMM reviews.
- Get employee feedback on EMM and the EMM solution via surveys.
- Introduce (new) employees to the EMM software through a training guide checklist.
- Create a process for employees to use if they’ve lost a device or suspect there’s been a data breach. ️♂️
- Ensure all your security-related recurring tasks are done properly.
- And many, many more possibilities!
Ready to take your organization’s enterprise mobility management to unprecedented levels?
Sign up for a free Process Street account and get started today.
Additional resources to bolster your organization’s security
You wouldn’t be here if you didn’t care about data, device, and network security management.
To assist your security-related endeavors even further (what can I say – we like being helpful here at Process Street!), underneath you’ll find a plethora of IT security processes. These are some of our most used templates, meaning there are tons of organizations already using these processes to keep data and devices secure.
Find our well-used privileged password management checklist below, followed by a list of 7 other super helpful, super useful templates and checklists.
- Network Administrator Daily Tasks
- Network Security Audit Checklist
- Firewall Audit Checklist
- VPN Configuration
- Apache Server Setup
- Email Server Security
- Penetration Testing
There you have it.
With the information provided in this post, your shiny new Process Street account, and the free templates you can make immediate use of, your organization’s corporate data will truly be kept out of harm’s way.
Are you new to EMM or are you a master of it? If you’re the latter, what tips and tricks would you like to share with the Process Street community? Write them in the comment box below!





